
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years

SCARS™ CYBER BASICS: Ransomware
Ransomware Is A Multi-Billion Dolar Industry
This document is written for more technical readers.
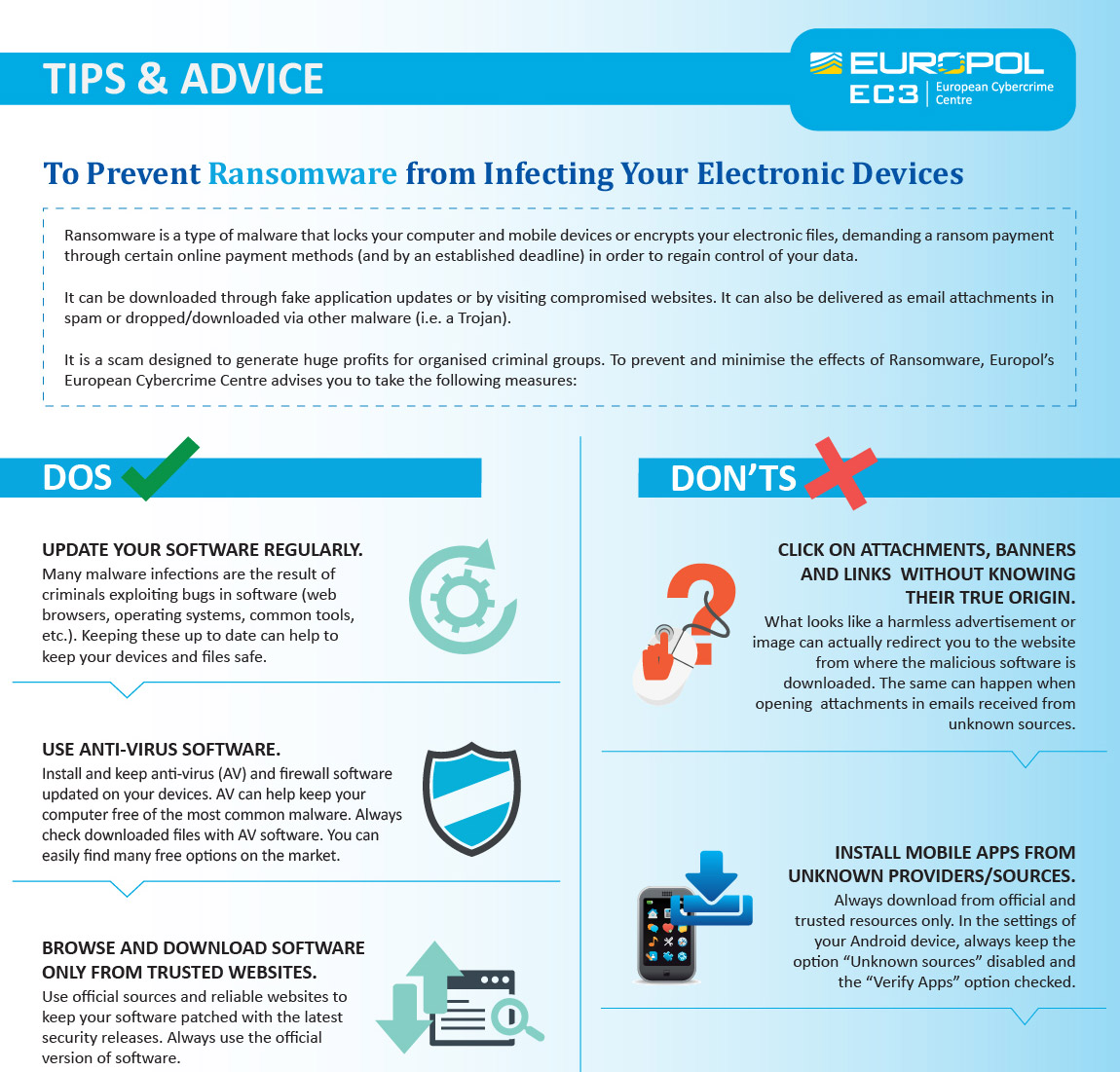
Ransomware is malware that locks your computer and mobile devices or encrypts your electronic files. When this happens, you can’t get to the data unless you pay a ransom.
HOWEVER, THIS IS NOT GUARANTEED AND YOU SHOULD NEVER PAY!
What Is Ransomware?
Ransomware is a type of malware that prevents you from accessing your computer (or the data that is stored on it). The computer itself may become locked, or the data on it might be stolen, deleted, or encrypted. Some ransomware will also try to spread to other machines on the network, such as the Wannacry malware that impacted the NHS in May 2017.
Normally you’re asked to make a payment (often demanded in a cryptocurrency such as Bitcoin), in order to unlock your computer (or to access your data). However, even if you pay the ransom, there is no guarantee that you will get access to your computer, or your files. Occasionally malware is presented as ransomware, but after the ransom is paid the files are not decrypted. This is known as wiper malware. For these reasons, it’s essential that you always have a recent offline backup of your most important files and data.
Should I Pay The Ransom?
Most entities generally advise not to pay the ransom, as there is no guarantee that you will get access to your device (or data).
Using A Defense In-Depth Strategy
Since there’s no way to completely protect your organization against malware infection, you should adopt a ‘defense-in-depth’ approach. This means using layers of defense with several mitigations at each layer. You’ll have more opportunities to detect malware, and then stop it before it causes real harm to your organization. You should assume that some malware will infiltrate your organization, so you can take steps to limit the impact this would cause, and speed up your response.
Getting Help – Helping Yourself
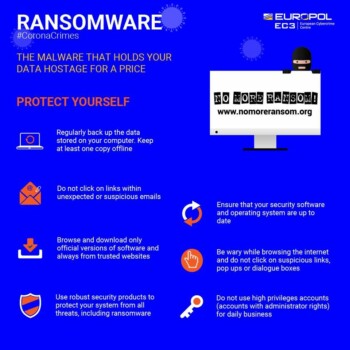
Interpol has collaborated on the creation of a central repository website for unlocking Ransomware at: www.nomoreransom.org
DECRYPTED RANSOMWARE
AVOIDING RANSOMWARE
Tip 1: Make Regular Backups
The key action to take to mitigate ransomware is to ensure that you have up-to-date backups of important files; if so, you will be able to recover your data without having to pay a ransom.
Make regular backups of your most important files – it will be different for every organization – and check that you know how to restore the files from the backup.
Ensure that a backup is kept separate from your network (‘offline’), or in a cloud service designed for this purpose – our blog on offline backups in an online world provides useful additional advice for organizations.
Cloud syncing services (like Dropbox, OneDrive and SharePoint, or Google Drive) should not be used as your only backup. This is because they may automatically synchronize immediately after your files have been ‘ransomwared’, and then you’ll lose your synchronized copies as well.
Make sure the device containing your backup (such as an external hard drive or a USB stick) is not permanently connected to your network and that you ideally have multiple copies. An attacker may choose to launch a ransomware attack when they know that the storage containing the backups is connected.
Tip 2: Prevent Malware From Being Delivered To Devices
You can reduce the likelihood of malicious content reaching your network through a combination of:
- filtering to only allow file types you would expect to receive
- blocking websites that are known to be malicious
- actively inspecting content
- using signatures to block known malicious code
These are typically done by network services rather than users’ devices. Examples include:
- mail filtering (in combination with spam filtering) which can block malicious emails and remove executable attachments
- intercepting proxies, which block known-malicious websites
- internet security gateways, which can inspect content in certain protocols (including some encrypted protocols) for known malware
- safe browsing lists within your web browsers which can prevent access to sites known to be hosting malicious content
Public sector organizations are encouraged to subscribe to the NCSC Protective DNS or similar services; this will prevent users from reaching known malicious sites.
Some ransomware attacks are deployed by attackers who have gained access to networks through remote access software like RDP. You should prevent attackers from being able to brute-force access to your networks through this (or similar) software by either:
- authenticating using Multi-Factor Authentication (MFA)
- ensuring users have first connected through a VPN that meets our recommendations.
Tip 3: Prevent Malware From Running On Devices
A ‘defense in depth’ approach assumes that malware will reach your devices. You should, therefore, take steps to prevent malware from running. The steps required will vary for each device type and OS, but in general, you should look to use device-level security features such as:
Centrally manage enterprise devices in order to either:
- only permit applications trusted by the enterprise to run on devices using technologies including AppLocker, or
- only permit the running of applications from trusted app stores (or other trusted locations)
Consider whether enterprise antivirus or anti-malware products are necessary, and keep the software (and its definition files) up to date.
Provide security education and awareness training to your people.
Disable or constrain macros in productivity suites, which means:
- disabling (or constraining) other scripting environments (e.g. PowerShell)
- disabling autorun for mounted media (prevent the use of removable media if it is not needed)
- protect your systems from malicious Microsoft Office macros
In addition, attackers can force their code to execute by exploiting vulnerabilities in the device. Prevent this by keeping devices well-configured and up to date. We recommend that you:
- install security updates as soon as they become available in order to fix exploitable bugs in your products.
- enable automatic updates for operating systems, applications, and firmware if you can
- use the latest versions of operating systems and applications to take advantage of the latest security features
- configure host-based and network firewalls, disallowing inbound connections by default
Tip 4: Limit The Impact Of Infection And Enable Rapid Response
If put in place, the following steps will ensure your incident responders can help your organization to recover quickly.
- Help prevent malware from spreading across your organization by preventing lateral movement. This will help because attackers aim to move across machines on the network. This might include targeting authentication credentials or perhaps abusing built-in tools.
- Use two-factor authentication (also known as 2FA) to authenticate users so that if malware steals credentials they can’t be reused.
- Ensure obsolete platforms (OS and apps) are properly segregated from the rest of the network.
- Regularly review and remove user permissions that are no longer required, to limit malware’s ability to spread. Malware can only spread to places on your network that infected users’ accounts have access to.
- System Administrators should avoid using their administrator accounts for email and web browsing, to avoid malware being able to run with their high levels of system privilege.
- Architect your network so that management interfaces are minimally exposed (our blog post on protecting management interfaces may help).
- Practice good asset management, including keeping track of which versions of the software are installed on your devices so that you can target security updates quickly if you need to.
- Keep your infrastructure patched, just as you keep your devices patched and prioritize devices performing a security-related function on your network (such as firewalls), and anything on your network boundary.
- Develop an incident response plan and exercise it.
Steps to take if your organization is already infected
If your organization has already been infected with malware, these steps may help limit the impact of the infection.
- Immediately disconnect the infected computers, laptops, or tablets from all network connections, whether wired, wireless or mobile phone-based.
- Consider whether turning off your Wi-Fi and disabling any core network connections (including switches) might be necessary in a very serious case.
- Reset credentials including passwords (especially for administrators) – but verify that you are not locking yourself out of systems that are needed for recovery.
- Safely wipe the infected devices and reinstall the operating system.
- Before you restore from a backup, verify that it is free from malware and ransomware. You should only restore from a backup if you are very confident that the backup is clean.
- Connect devices to a clean network in order to download, install, and update the operating system and all other software.
- Install, update, and run antivirus software.
- Reconnect to your network.
- Monitor network traffic and run antivirus scans to identify if any infection remains.
Note: Files encrypted by most ransomware have no way of being decrypted by anyone other than the attacker. Don’t waste your time or money on services that promise to do it. In some cases, security professionals have produced tools that can decrypt files due to weaknesses in the malware (which may be able to recover some data), but you should take precautions before running unknown tools on your devices.
Further Advice
IN THE UNITED KINGDOM
- The National Crime Agency encourages anyone who thinks they may have been subject to online fraud to contact Action Fraud at https://www.actionfraud.police.uk.
- The National Cyber Security Centre (NCSC) runs a commercial scheme called Cyber Incident Response, where certified companies provide crisis support to affected organizations.
- The Cyber Security Information Sharing Partnership (CiSP) offers organizations in the UK a safe portal in which to discuss and share intelligence that can assist the community and raise the UK’s cyber resilience. We encourage our members to share technical information and indicators of compromise so that the effects of new malware, and particularly ransomware, can be largely reduced.
- You may also wish to consider the Cyber Essentials certification scheme (which covers a number of these mitigations) so your customers and partners can see that you have addressed these risks. Many of these mitigations also work well against other types of attacks, such as phishing.
- Consider following the NCSC guidance on protecting your organization from phishing attacks.
- Learn more here: https://www.ncsc.gov.uk/guidance/mitigating-malware-and-ransomware-attacks
IN THE UNITED STATES
- Contact your local FBI office immediately to report the ransomware attack and follow their guidance.
- If you are able to recover be sure to report the ransomware attack on the FBI’s www.IC3.gov
TAGS: SCARS, Important Article, Information About Scams, Anti-Scam, Scams, Scammers, Fraudsters, Cybercrime, Crybercriminals, Ransomeware, Scam Victims, Malware, Ransomware Attack, Infection
SCARS™ Editorial Team
Society of Citizens Against Relationship Scams Inc.
A Worldwide Crime Victims Assistance Nonprofit Organization
Visit: www.AgainstScams.org
Contact Us: Contact@AgainstScams.org
PLEASE SHARE OUR ARTICLES WITH YOUR FRIENDS & FAMILY
HELP OTHERS STAY SAFE ONLINE – YOUR KNOWLEDGE CAN MAKE THE DIFFERENCE!
The Latest SCARS Posts:
FIND MORE SCAM NEWS
«SCAMCRIME.COM»
JOIN US ON FACEBOOK
«CLICK HERE»
END
MORE INFORMATION
– – –
Tell us about your experiences with Romance Scammers in our
« Scams Discussion Forum on Facebook »
– – –
FAQ: How Do You Properly Report Scammers?
It is essential that law enforcement knows about scams & scammers, even though there is nothing (in most cases) that they can do.
Always report scams involving money lost or where you received money to:
- Local Police – ask them to take an “informational” police report – say you need it for your insurance
- U.S. State Police (if you live in the U.S.) – they will take the matter more seriously and provide you with more help than local police
- Your National Police or FBI « www.IC3.gov »
- The SCARS|CDN™ Cybercriminal Data Network – Worldwide Reporting Network on « www.Anyscam.com »
This helps your government understand the problem, and allows law enforcement to add scammers on watch lists worldwide.
– – –
To learn more about SCARS visit « www.AgainstScams.org »
Please be sure to report all scammers
on « www.Anyscam.com »
Disclaimer:
SCARS IS A DIGITAL PUBLISHER AND DOES NOT OFFER HEALTH OR MEDICAL ADVICE, LEGAL ADVICE, FINANCIAL ADVICE, OR SERVICES THAT SCARS IS NOT LICENSED OR REGISTERED TO PERFORM.
IF YOU’RE FACING A MEDICAL EMERGENCY, CALL YOUR LOCAL EMERGENCY SERVICES IMMEDIATELY, OR VISIT THE NEAREST EMERGENCY ROOM OR URGENT CARE CENTER. YOU SHOULD CONSULT YOUR HEALTHCARE PROVIDER BEFORE FOLLOWING ANY MEDICALLY RELATED INFORMATION PRESENTED ON OUR PAGES.
ALWAYS CONSULT A LICENSED ATTORNEY FOR ANY ADVICE REGARDING LEGAL MATTERS.
A LICENSED FINANCIAL OR TAX PROFESSIONAL SHOULD BE CONSULTED BEFORE ACTING ON ANY INFORMATION RELATING TO YOUR PERSONAL FINANCES OR TAX RELATED ISSUES AND INFORMATION.
This content and other material contained on the website, apps, newsletter, and products (“Content”), is general in nature and for informational purposes only and does not constitute medical, legal, or financial advice; the Content is not intended to be a substitute for licensed or regulated professional advice. Always consult your doctor or other qualified healthcare provider, lawyer, financial or tax professional with any questions you may have regarding the educational information contained herein. SCARS makes no guarantees about the efficacy of information described on or in SCARS’s Content. The information contained are subject to change and are not intended to cover all possible situations or effects. SCARS does not recommend or endorse any specific professional or care provider, product, service, or other information that may be mentioned in SCARS’s websites, apps, and Content unless explicitly identified as such.
The disclaimers herein are provided on this page for ease of reference. These disclaimers supplement and are a part of SCARS’s websites Terms of Use.
Legal Notices:
All original content is Copyright © 1991 – 2020 Society of Citizens Against Relationship Scams Inc. (D.B.A SCARS) All Rights Reserved Worldwide & Webwide. Third-party copyrights acknowledge.
SCARS, SCARS|INTERNATIONAL, SCARS, SCARS|SUPPORT, SCARS, RSN, Romance Scams Now, SCARS|WORLDWIDE, SCARS|GLOBAL, SCARS, Society of Citizens Against Relationship Scams, Society of Citizens Against Romance Scams, SCARS|ANYSCAM, Project Anyscam, Anyscam, SCARS|GOFCH, GOFCH, SCARS|CHINA, SCARS|CDN, SCARS|UK, SCARS|LATINOAMERICA, SCARS|MEMBER, SCARS|VOLUNTEER, SCARS Cybercriminal Data Network, Cobalt Alert, Scam Victims Support Group, are all trademarks of Society of Citizens Against Relationship Scams Inc.
Contact the law firm for the Society of Citizens Against Relationship Scams Incorporated by email at legal@AgainstScams.org
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Scott V. on The Persistence of Danielle Delaunay as a Fake Identity – 2026: “That was the woman they used with me!! They were able to send a video of her talking on one…” Jun 2, 16:02
- on The Persistence of Danielle Delaunay as a Fake Identity – 2026: “That’s sad but they do a lot” Jun 2, 14:39
- on Major General William Burke Garrett III – Another Stolen Identity Used To Scam Women: “I am from Guatemala. I was contacted by William Barret two weeks ago, who mentioned that he was a widower…” May 21, 17:13
- on Scam Grooming: Finding Common Interests: “I’ve been groomed for two months then the love bombing started. This guy was supposedly a Ukrainian soldier stationed in…” May 8, 13:56
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I was just very numb after my scam, I barely slept and was exhausted. I wish I had know about…” May 7, 22:31
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I can barely handle myself these days so even thinking about another relationship is too much for me. The time…” May 7, 20:59
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “Thank you! I understand that these impulse reactions can affect us for some time. And another relationship especially soon after…” May 7, 18:14
- on Reporting Scams To The United States Secret Service – Cryptocurrency Recovery – Forget The FBI! [VIDEO]: “Unfortunately, the Federal services tend to aggregate crimes together rather than investigate individual offenses when it comes to scams.” May 6, 01:57
- on Romance Scams Detection Training Tool – 2026: “Criminals are not toys, and they can harm you in ways you can’t even imagine.” May 6, 01:55
- on Romance Scams Detection Training Tool – 2026: “Great, word, by word as it is happening to me right now however I already stated clearly that I have…” May 2, 20:06
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.






















Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.