Do You Need Support?
Get It Now!
SCARS provides the leading Support & Recovery program for relationship scam victims – completely FREE!
Our managed peer support groups allow victims to talk to other survivors and recover in the most experienced environment possible, for as long as they need. Recovery takes as long as it takes – we put no limits on our support!
SCARS is the most trusted support & education provider in the world. Our team is certified in trauma-informed care, grief counseling, and so much more!
To apply to join our groups visit support.AgainstScams.org
We also offer separate support groups for family & friends too.
Become a
SCARS STAR™ Member
SCARS offers memberships in our STAR program, which includes many benefits for a very low annual membership fee!
SCARS STAR Membership benefits include:
- FREE Counseling or Therapy Benefit from our partner BetterHelp.com
- Exclusive members-only content & publications
- Discounts on SCARS Self-Help Books Save
- And more!
To learn more about the SCARS STAR Membership visit membership.AgainstScams.org
To become a SCARS STAR Member right now visit join.AgainstScams.org
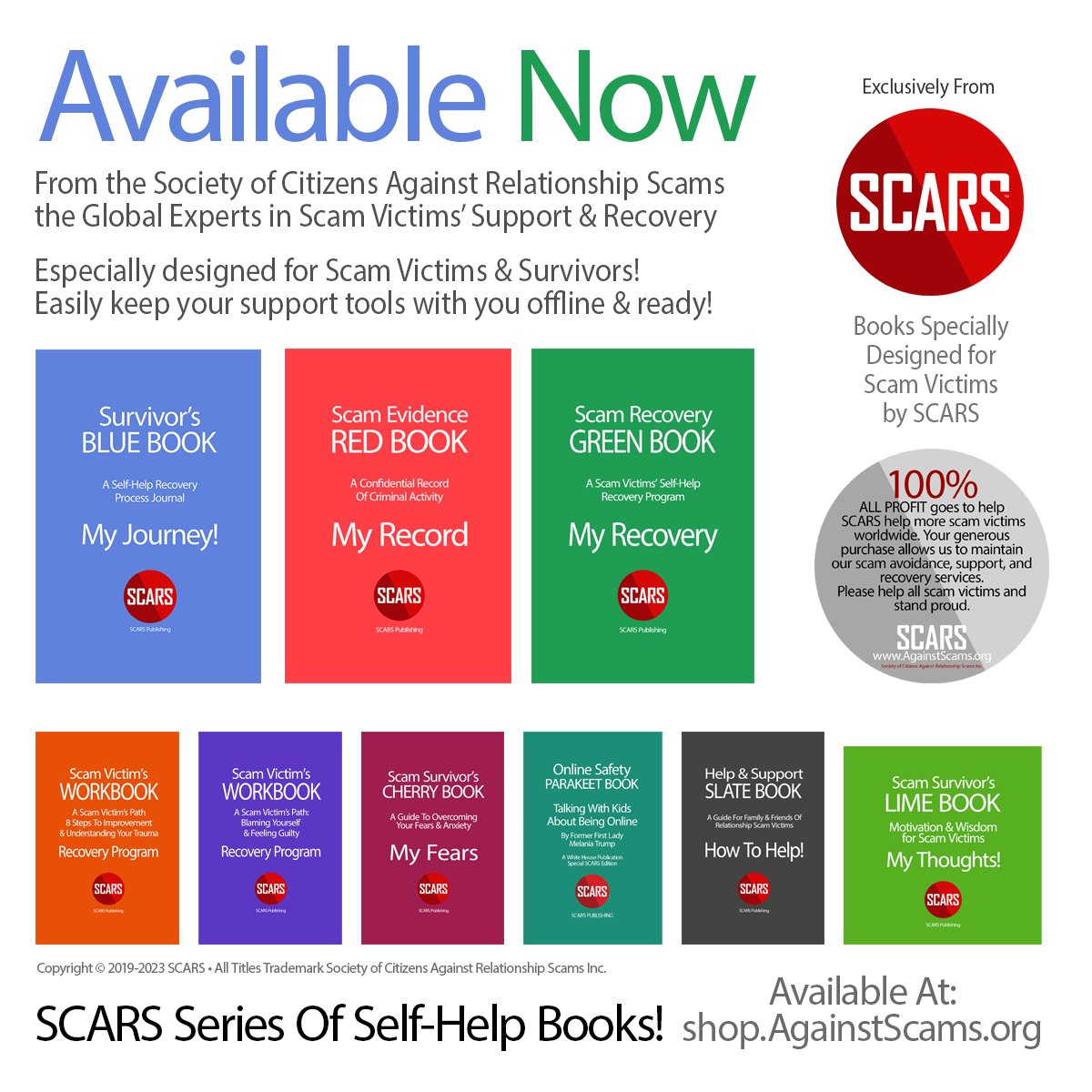
Scam Victim Self-Help Do-It-Yourself Recovery Books
SCARS Printed Books For Every Scam Survivor From SCARS Publishing
Visit shop.AgainstScams.org
Each is based on our SCARS Team’s 32-plus years of experience.
SCARS Website Visitors receive an Extra 10% Discount
Use Discount Code “romanacescamsnow” at Checkout
To Learn More Also Look At Our Article Catalogs
Scam & Crime Types
More SCARS
- ScamsNOW Magazine – ScamsNOW.com
- ContraEstafas.org
- ScammerPhotos.com
- AnyScam.com – reporting
- AgainstScams.org – SCARS Corporate Website
- SCARS YouTube Video Channel
Updated SCARS RomanceScamsNow.com Posts:
FIND SCAMMER PHOTOS ON
ScammerPhotos.com
FIND SCARS ON FACEBOOK
CLICK HERE
Legal Disclaimer:
The content provided on this platform regarding psychological topics is intended solely for educational and entertainment purposes. The publisher makes no representations or warranties regarding the accuracy or completeness of the information presented. The content is designed to raise awareness about various psychological subjects, and readers are strongly encouraged to conduct their own research and verify information independently.
The information presented does not constitute professional advice, diagnosis, or treatment of any psychological disorder or disease. It is not a substitute for professional medical or mental health advice, diagnosis, or treatment. Readers are advised to seek the guidance of a licensed medical professional for any questions or concerns related to their mental health.
The publisher disclaims any responsibility for actions taken or not taken based on the content provided. The treatment of psychological issues is a serious matter, and readers should consult with qualified professionals to address their specific circumstances. The content on this platform is not intended to create, and receipt of it does not constitute, a therapist-client relationship.
Interpretation and Definitions
Definitions
For the purposes of this Disclaimer:
- Company (referred to as either “the Company”, “We”, “Us” or “Our” in this Disclaimer) refers to Society of Citizens Against Relationship Scams Inc. (registered d.b.a. “SCARS”,) 9561 Fountainbleau Blvd., Suit 602, Miami FL 33172.
- Service refers to the Website.
- You means the individual accessing this website, or the company, or other legal entity on behalf of which such individual is accessing or using the Service, as applicable.
- Website refers to RomanceScamsNOW.com, accessible from https://romancescamsnow.com
Website Disclaimer
The information contained on this website is for general information purposes only.
The Company assumes no responsibility for errors or omissions in the contents of the Service.
In no event shall the Company be liable for any special, direct, indirect, consequential, or incidental damages or any damages whatsoever, whether in an action of contract, negligence or other tort, arising out of or in connection with the use of the Service or the contents of the Service. The Company reserves the right to make additions, deletions, or modifications to the contents on the Service at any time without prior notice.
The Company does not warrant this website in any way.
External Links Disclaimer
This website may contain links to external websites that are not provided or maintained by or in any way affiliated with the Company.
Please note that the Company does not guarantee the accuracy, relevance, timeliness, or completeness of any information on these external websites.
Errors and Omissions Disclaimer
The information given by SCARS is for general guidance on matters of interest only. Even if the Company takes every precaution to ensure that the content of this website is both current and accurate, errors can occur. Plus, given the changing nature of laws, rules, and regulations, there may be delays, omissions, or inaccuracies in the information contained on this website.
SCARS is not responsible for any errors or omissions, or for the results obtained from the use of this information.
Fair Use Disclaimer
SCARS may use copyrighted material that has not always been specifically authorized by the copyright owner. The Company is making such material available for criticism, comment, news reporting, teaching, scholarship, or research.
The Company believes this constitutes a “fair use” of any such copyrighted material as provided for in section 107 of the United States Copyright law.
If You wish to use copyrighted material from this website for your own purposes that go beyond fair use, You must obtain permission from the copyright owner.
Views Expressed Disclaimer
The Service may contain views and opinions which are those of the authors and do not necessarily reflect the official policy or position of any other author, agency, organization, employer, or company, including SCARS.
Comments published by users are their sole responsibility and the users will take full responsibility, liability, and blame for any libel or litigation that results from something written in or as a direct result of something written in a comment. The Company is not liable for any comment published by users and reserves the right to delete any comment for any reason whatsoever.
No Responsibility Disclaimer
The information on the Service is provided with the understanding that the Company is not herein engaged in rendering legal, accounting, tax, medical or mental health, or other professional advice and services. As such, it should not be used as a substitute for consultation with professional accounting, tax, legal, medical or mental health, or other competent advisers.
In no event shall the Company, its team, board of directors, volunteers, or its suppliers be liable for any special, incidental, indirect, or consequential damages whatsoever arising out of or in connection with your access or use or inability to access or use the Service.
“Use at Your Own Risk” Disclaimer
All information on this website is provided “as is”, with no guarantee of completeness, accuracy, timeliness or of the results obtained from the use of this information, and without warranty of any kind, express or implied, including, but not limited to warranties of performance, merchantability, and fitness for a particular purpose.
SCARS will not be liable to You or anyone else for any decision made or action taken in reliance on the information given by the Service or for any consequential, special, or similar damages, even if advised of the possibility of such damages.
Contact Us
If you have any questions about this Disclaimer, You can contact Us:
- By email: contact@AgainstScams.org
PLEASE NOTE: Psychology Clarification
The following specific modalities within the practice of psychology are restricted to psychologists appropriately trained in the use of such modalities:
- Diagnosis: The diagnosis of mental, emotional, or brain disorders and related behaviors.
- Psychoanalysis: Psychoanalysis is a type of therapy that focuses on helping individuals to understand and resolve unconscious conflicts.
- Hypnosis: Hypnosis is a state of trance in which individuals are more susceptible to suggestion. It can be used to treat a variety of conditions, including anxiety, depression, and pain.
- Biofeedback: Biofeedback is a type of therapy that teaches individuals to control their bodily functions, such as heart rate and blood pressure. It can be used to treat a variety of conditions, including stress, anxiety, and pain.
- Behavioral analysis: Behavioral analysis is a type of therapy that focuses on changing individuals’ behaviors. It is often used to treat conditions such as autism and ADHD.
Neuropsychology: Neuropsychology is a type of psychology that focuses on the relationship between the brain and behavior. It is often used to assess and treat cognitive impairments caused by brain injuries or diseases.
SCARS and the members of the SCARS Team do not engage in any of the above modalities in relationship to scam victims. SCARS is not a mental healthcare provider and recognizes the importance of professionalism and separation between its work and that of the licensed practice of psychology.
SCARS is an educational provider of generalized self-help information that individuals can use for their own benefit to achieve their own goals related to emotional trauma. SCARS recommends that all scam victims see professional counselors or therapists to help them determine the suitability of any specific information or practices that may help them.
SCARS cannot diagnose or treat any individuals, nor can it state the effectiveness of any educational information that it may provide, regardless of its experience in interacting with traumatized scam victims over time. All information that SCARS provides is purely for general educational purposes to help scam victims become aware of and better understand the topics and to be able to dialog with their counselors or therapists.
It is important that all readers understand these distinctions and that they apply the information that SCARS may publish at their own risk, and should do so only after consulting a licensed psychologist or mental healthcare provider.
SCARS IS A DIGITAL PUBLISHER AND DOES NOT OFFER HEALTH OR MEDICAL ADVICE, LEGAL ADVICE, FINANCIAL ADVICE, OR SERVICES THAT SCARS IS NOT LICENSED OR REGISTERED TO PERFORM.
IF YOU’RE FACING A MEDICAL EMERGENCY, CALL YOUR LOCAL EMERGENCY SERVICES IMMEDIATELY, OR VISIT THE NEAREST EMERGENCY ROOM OR URGENT CARE CENTER. YOU SHOULD CONSULT YOUR HEALTHCARE PROVIDER BEFORE FOLLOWING ANY MEDICALLY RELATED INFORMATION PRESENTED ON OUR PAGES.
ALWAYS CONSULT A LICENSED ATTORNEY FOR ANY ADVICE REGARDING LEGAL MATTERS.
A LICENSED FINANCIAL OR TAX PROFESSIONAL SHOULD BE CONSULTED BEFORE ACTING ON ANY INFORMATION RELATING TO YOUR PERSONAL FINANCES OR TAX RELATED ISSUES AND INFORMATION.
SCARS IS NOT A PRIVATE INVESTIGATOR – WE DO NOT PROVIDE INVESTIGATIVE SERVICES FOR INDIVIDUALS OR BUSINESSES. ANY INVESTIGATIONS THAT SCARS MAY PERFORM IS NOT A SERVICE PROVIDED TO THIRD-PARTIES. INFORMATION REPORTED TO SCARS MAY BE FORWARDED TO LAW ENFORCEMENT AS SCARS SEE FIT AND APPROPRIATE.
This content and other material contained on the website, apps, newsletter, and products (“Content”), is general in nature and for informational purposes only and does not constitute medical, legal, or financial advice; the Content is not intended to be a substitute for licensed or regulated professional advice. Always consult your doctor or other qualified healthcare provider, lawyer, financial, or tax professional with any questions you may have regarding the educational information contained herein. SCARS makes no guarantees about the efficacy of information described on or in SCARS’ Content. The information contained is subject to change and is not intended to cover all possible situations or effects. SCARS does not recommend or endorse any specific professional or care provider, product, service, or other information that may be mentioned in SCARS’ websites, apps, and Content unless explicitly identified as such.
The disclaimers herein are provided on this page for ease of reference. These disclaimers supplement and are a part of SCARS’ website’s Terms of Use.
All original content is Copyright © 1991 – 2023 Society of Citizens Against Relationship Scams Inc. (Registered D.B.A SCARS) All Rights Reserved Worldwide & Webwide. Third-party copyrights acknowledge.
U.S. State of Florida Registration Nonprofit (Not for Profit) #N20000011978 [SCARS DBA Registered #G20000137918] – Learn more at www.AgainstScams.org
Contact the law firm for the Society of Citizens Against Relationship Scams Incorporated by email at legal@AgainstScams.org