
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years

According To Industry Sources, Cyber-Enabled Criminals Are Constantly Inventing New Attack Types
As scammers apply more institutional knowledge of the internet and online user’s behaviors they adapt their tactics. They are not giving up on the old techniques, but expanding to find more ways to scam victims – both individuals and corporations – from their money.
Here are the latest types of socially engineered scams running worldwide:
Social Engineering Against All Users
1: Browser Notification Hijack
Web sites have for several years asked visitors to approve “notifications” from the site. We do that on this website, but we use a reliable and secure partner to manage that (specifically OneSignal – an industry leader). Not all websites do use reliable partners – those that try to do it themselves can be vulnerable.
What was once a useful way to engage with readers and keep them up to date can be compromised and turned into a social engineering tool.
These are called push notifications, and they are valuable, but they can be weaponized on poorly managed websites. The problem is that many users blindly click ‘yes’ to allow these notifications. While many users have learned some level of caution with web browsers, the notifications appear more like system messages from the device itself, rather than the browser.
In our case, we offer that choice, but we also allow you to subscribe to our newsletter so you don’t have to use the push notifications- this is a safer alternative for most websites – unless they know what they are doing.
Once the cybercriminal has a user’s consent, they start inundating them with alert messages – and the messages are usually phishing schemes or scam notifications that contain malware.
Rule of thumb: if you receive more than a couple of alerts a day – you probably do not want their alerts anyway.
2: Deepfake Recordings
Social engineers are now using deepfakes – very realistic recordings that use artificial intelligence to simulate a specific person’s appearance or voice – to trick victims into divulging information or performing an action that benefits the scammer.
This means they can send better fake videos to victims of romance scams, etc. It also means they can fabricate fake adult intimate videos and photos for sextortion purposes with ease.
Audio deepfakes – in which the cybercriminal uses a “cloned” voice that is nearly indistinguishable from a real person’s voice to create a scam audio recording – are a real growing concern.
One of the earliest successful examples came in 2019, when a fake recording of a CEO’s voice was used to instruct an employee to immediately transfer money to an international account. The recording was left as a voicemail to the subordinate, who obeyed the fraudulent instructions and sent $243,000 to the attackers.
We are seeing criminals use deepfake recordings to company manipulate staff into sending money or offering up private information – only audio recordings so far, but Gerchow believes video deepfakes are just a matter of time. But these are also being used in other kinds of scams, such as romance scams.
Everyone needs to become much smarter and more knowledgeable fast.
3: Malicious QR Codes
QR code-related phishing fraud has become common in the last year.
QR codes – those machine-readable, black-and-white matrix codes arranged in a square – have become an increasingly popular way for companies to engage with consumers and deliver services in the midst of COVID-19. For example, many restaurants have ditched paper menus, and instead, allow patrons to scan a QR code with their smartphone. Similarly, many Girl Scouts posted QR codes for no-contact ordering and delivery of cookies this spring.
Here is the problem – you cannot see what web address the QR Code contains just by looking at it!
Many of the websites that QR codes send people to are operated by third-party vendors. When scanned, a malicious QR code can connect phones to a malicious destination – just like clicking on a bad link. Same concept; new wrapper.
QR Codes that appear on ads or other marketing material can offer everything from a menu, to access to a website, to a chance of winning an Xbox. Always look for a real web address and always be cautious. Only trust reliable sources.
4: Text fraud
Text messages have been a conduit for social engineering scams for a while, but texting tactics becoming very common and frequent.
A large portion of the population prefers communicating via text messages as opposed to the phone. People are now extremely used to communicating very confidential types of information via text and it comes with risks.
Because grocery and food delivery has grown in the last year, delivery-related scam texts are up. Other common lures include texts that promise information about COVID stimulus checks that link victims back to a website that looks like the IRS site and asks for sensitive personal information, such as a birth date and social security number.
If you get a questionable text, look at the sending number – have you seen it before? Do a quick search online and see what shows.
As with QR codes, victims simply have not developed the level of awareness and caution needed.
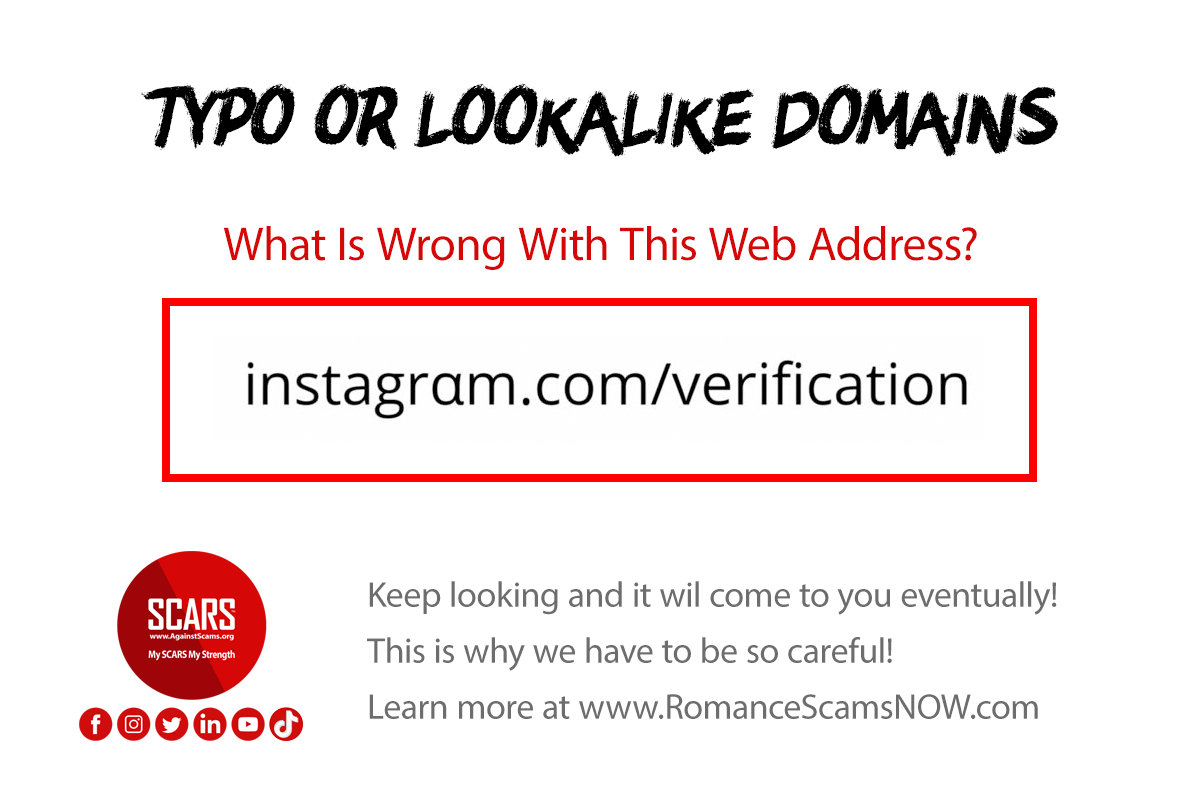
5: Typo-squatting or Lookalike Domains
This is actually not new but has become more sinister in the last year.
A Typo Domain uses common misspellings of a domain name that many people would naturally make. Mostly these have been used to gain ad exposures from people carelessly typing a web address. But increasingly they are used to fool victims in email addresses, or in directing unsuspecting victims to fake or malicious websites.
For example: think Gooogle instead of Google, or by adding a different top-level domain (.uk instead of .co.uk). Unlike the often sloppy versions from earlier days, today these sites may feature sophisticated designs, carefully detailed mimicry of legitimate sites, and sophisticated functionality.
Lookalike domains – are often served up in a business email compromise (BEC) attack. Fraudsters impersonate legitimate domains in order to fool victims into thinking they are in a safe location or that an email is legitimate.
We saw an example of this from a scammer in Australia that used the name of a government anti-scam agency called “ScamWatch” in a domain name to fool scam victims into believing they were dealing with the government investigators. They were asked to pay an investigation fee. SCARS has it shut down in 2019, but criminals persist in creating fake businesses.
A perfect example – can you see what is wrong in this web address?
Social engineering victims are usually tricked into either feeling psychological safety by their choice or into seeking psychological safety in a way that will play into a criminal’s hands.
Criminals set up these sites not only to deliver malware but also to capture credit card information or other sensitive data through fake login fields or other fake forms.
Social Engineering Against Businesses
1: Supply Chain Partner Impersonation
Attacks that exploit parts of an organization’s supply chain are now a big problem. This is basically a variation of BEC scams, but scammers now have more than enough money to understand real business processes.
It’s not easy to defend what you can’t see, and you are only as strong as the weakest link. For example, there have been many targeted emails coming in that look like they are from your trusted partners but are in fact bad actors posing as employees you may know within your network.
Always verify, verify, verify. Create a new email from the address in your contact list, or through your connection on LinkedIn. Do not just reply to a message you receive.
These attacks have become even more detailed and sophisticated over time. They will look and sound good.
We see these long, sophisticated attempts to build trust or relationships with a company’s outbound-facing teams whose entire job is to help.
By establishing these trusted relationships, the criminals’ ultimate goal is to make standard social engineering tactics more effective, eliciting help in bypassing security controls, or sending malware or gaining information that will compromise the target company’s systems.
The SolarWinds attack is an example of a supply chain attack – in that case, a specific version called a vendor email compromise attack (VEC) was used. As SolarWinds officials noted, an email account was compromised and used to programmatically access accounts of targeted SolarWinds personnel in business and technical roles.
2: Collaboration Scams
With this social engineering tactic, cybercriminals target professionals in collaborative fields, including designers, developers, and even security researchers. The lure is an invitation that asks them to collaborate on work via an app or website.
Recent pandemic lockdowns and expanded work-from-home increased people’s comfort with remote collaboration, so this tactic fit the times well.
The cybercriminal sends over a Visual Studio Project containing malicious code. The user runs the program, and their device is infected pretty quickly. This attack essentially exploits the desire or need to assist or help others with passion projects.
Obviously, you should never accept or open an email or other attachments from people that you do not know! And never run anything that can be executed on your computer.
These attacks are often well-crafted, showing great attention to detail – but especially for people that live on the web – they should know better!
Criminals posed as active researchers and built social proof documents – with apparent third parties validating their research – using a blog including articles from industry sources as ‘guest posts,’ Twitter accounts, YouTube videos, LinkedIn, Discord, and more, A suspicious victim may be put at ease by this seemingly wide social footprint. But like all things online, don’t trust anyone!
If someone wants to participate in research then do it through a known channel such as RsearchGate.
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Laura Schultz on Scam Grooming: Finding Common Interests: “I’ve been groomed for two months then the love bombing started. This guy was supposedly a Ukrainian soldier stationed in…” May 8, 13:56
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I was just very numb after my scam, I barely slept and was exhausted. I wish I had know about…” May 7, 22:31
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I can barely handle myself these days so even thinking about another relationship is too much for me. The time…” May 7, 20:59
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “Thank you! I understand that these impulse reactions can affect us for some time. And another relationship especially soon after…” May 7, 18:14
- on Reporting Scams To The United States Secret Service – Cryptocurrency Recovery – Forget The FBI! [VIDEO]: “Unfortunately, the Federal services tend to aggregate crimes together rather than investigate individual offenses when it comes to scams.” May 6, 01:57
- on Romance Scams Detection Training Tool – 2026: “Criminals are not toys, and they can harm you in ways you can’t even imagine.” May 6, 01:55
- on Romance Scams Detection Training Tool – 2026: “Great, word, by word as it is happening to me right now however I already stated clearly that I have…” May 2, 20:06
- on Bank Impersonation Scams – 2026: “Great article, great detail, great reminders, Thank You SCARS. Scammers’ tactics unfortunately are advancing at the speed of light. I…” May 1, 13:27
- on Why Do Police Try To Avoid Taking Reports For Scams?: “My local police department has been responsive (Palm Beach Sheriffs Office). I wish I could say the same thing about…” Apr 30, 15:35
- on Reporting Scams To The United States Secret Service – Cryptocurrency Recovery – Forget The FBI! [VIDEO]: “I reported my fraud to the FBI and Secret Service as soon as I finished up my IC3 report. I…” Apr 30, 15:29
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.














Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.