
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years

A Systematic Approach for Investigating Criminal Networks
Based on the work By Jennifer A. Johnson, Ph.D., John David Reitzel, Ph.D., Bryan F. Norwood, David M. McCoy, D. Brian Cummings, and Renee R. Tate, courtesy of the United States Federal Bureau of Investigation
“Social network analysis provides a systematic approach for investigating large amounts of data on people and relationships.”
What is Social network analysis (SNA)?
Social Network Analysis (SNA) is often confused with social networking sites, such as Facebook, when in fact, SNA is an analytical tool that can be used to map and measure social relationships.
Through quantitative metrics and robust visual displays, police can use SNA to discover, analyze, and visualize the social networks of criminal suspects.
In the case of online criminals, it can allow anyone to map out the scope of a criminal; organization and those that are connected with it. In short, it can help identify other criminals by their connection to a single criminal
A Methodology
SNA is a social science methodology, and it serves as a valuable tool for law enforcement or anyone interested in criminology or crime prevention. While technologically sophisticated, SNA proves easy to use and employ. Using available data, police departments structure the examination of an offender’s social network in ways not previously conceivable.
Manual examination of social networks tends to be difficult, time-consuming, and arbitrary, making it more prone to error. SNA provides a systematic approach for investigating large amounts of data points on people and relationships. It improves law enforcement effectiveness and efficiency by using complex information regarding individuals socially related to suspects. This often leads to improved clearance rates for many crimes and the development of better crime prevention strategies.
But in the case of online criminals, it also helps us to identify the other criminals that are involved in these crimes by their connections to a starting point suspect.
For example:
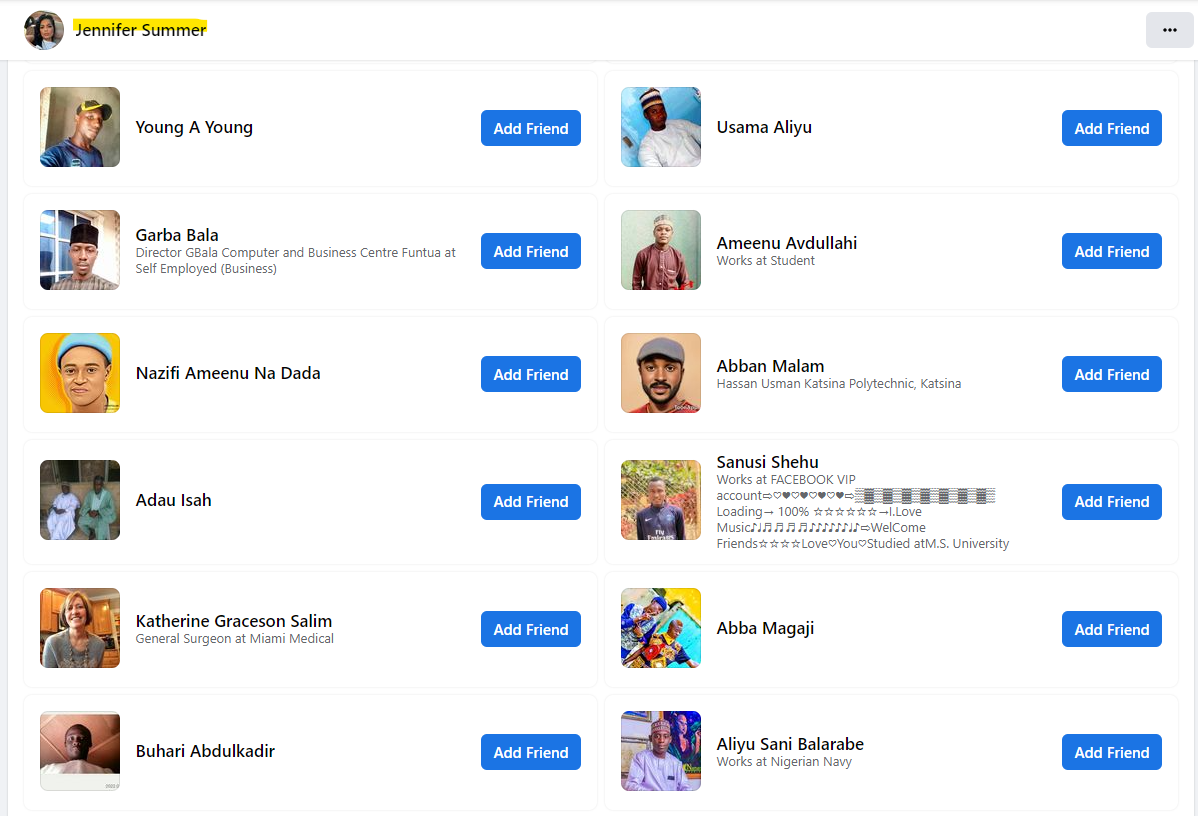
Use Case #1: you find a fake profile on Facebook – using stolen photos to impersonate someone for the purpose of scamming others. You are able to see their friends list and you see a number of out-of-the-ordinary friends. By out-of-the-ordinary we mean abnormal connections. This is our first link in identifying the probable real criminals that created this fake profile or those that are part of the creators’ criminal network. This allows each of these criminals to be identified to law enforcement or other crime prevention organizations (such as SCARS) for action.
Use Case #2: you find a fake profile on Facebook – using stolen photos to impersonate someone for the purpose of scamming others. You are NOT able to see their friends list. So in this case you look at the people commenting of posts in the profile. Against you see a number of out-of-the-ordinary friends.
Use Case #3: you find a group that is run by scammers, and you can go through the members (or at least the admins) and then follow down to their profiles and perform the same analysis.
What Can You Find?
Typically, if you are observant you will see that a given profile is connected to hundreds or thousands of other criminals. You will be able to trace each one down and then look at their friends and followers, so on and so forth. From just a single profile you can identify thousands of real criminals and the fake profiles they create.
What you do with them will be the key!
At a minimum, report each one to the platform (Facebook, Instagram, WhatsApp, etc.). Additionally, if they are real criminals we ask that you report them on www.Anyscam.com for further analysis and notification to law enforcement.
It’s Value
SNA derives its value from human organization and social interaction for criminal and noncriminal purposes. Social networks sometimes promote illegal behavior (e.g., scams and online crime) among related offenders across criminal domains. They can provide a source for cybercrime and related services distribution, other crimes such as human trafficking, and even international terrorism. The networks may supply an essential first insight for many serious criminal behaviors.
Social networks that enable crime are not mutually exclusive from the networks of law-abiding citizens. They are interspersed within these communities, drawing support from residents and extracting significant costs from host neighborhoods. The influence of social networks in producing criminal behavior indicates that effective crime-fighting strategies are contingent upon law enforcement and crime prevention organizations’ ability to identify and respond appropriately to the networks where the behavior is embedded.
“Social networks that enable crime are not mutually exclusive from the networks of law-abiding citizens.”
SNA Theory and Method
SNA is a theory about how humans organize and a method to examine such organization. The approach indicates that actors are positioned in and influenced by a larger social network. Methodologically, it provides a precise, quantitative tool through which agencies can identify, map, and measure relationship patterns.
Three points of data—two actors and the tie or link between them—comprise the basic unit of analysis.
Actors “nodes” are people, organizations, computers, or any other entity that processes or exchanges information or resources. Relationships “ties, connections, or edges” between nodes represent types of exchange, such as drug transactions between a seller and buyer, phone calls between two terrorists, or contacts between victims and offenders. SNA focuses on both positive and negative relationships between sets of individuals.
This analysis produces two forms of output, one visual and the other mathematical. The visual consists of a map or rendering of the network, called a social network diagram, which displays the nodes and relationships between them. In larger networks, key nodes are more difficult to identify; therefore, the analysis turns to the quantitative output of SNA.
A Simple Approach: When we are talking about scammers online, you can use their page of friends as your diagram. You can save the whole friends page and an HTML page on your laptop or you can highlight and copy all of the friends into a spreadsheet.
The centrality of nodes, such as those representing offenders, identifies the prominence of persons to the overall functioning of the network. It indicates their importance to the criminal system, role, level of activity, control over the flow of information, and relationships. Basic centrality metrics provide further details. “Degree” gauges how many connections a particular node possesses, “betweenness” measures how important it is to the flow, and “closeness” indicates how quickly the node accesses information from the network. Nodes are rank-ordered according to their centrality, with those at the top playing the most prominent role. These measures cannot tell an analyst what the structure should be, but they can elaborate on the actual makeup of the network. The value and actionable intelligence of each of these metrics is determined by the information the analyst wants.
Analysis Tip: in the case of scammers, look for the oldest obvious scammers (by age) in a friend’s list – they are most likely to be the chief of the scammer’s pyramid structure – in other words, the most important and probably the king pin!
“Remember this is a powerful tool, but in the case of scammers we can use a simpler form of it still with great results!”
Conclusion
Law enforcement agencies have come a long way from pinpoint mapping. The technological advancements in recent years can provide personnel more confidence to handle complex crime problems confronting departments around the country. Social network analysis demonstrated its utility and effectiveness as a means of solving crimes or determining persons of interest and bridging the gap between crime analysts and police officers in the field. With the support of robust technology, SNA becomes reliable across time, data, analysts, and networks and quickly produces actionable results inside any operational law enforcement environment.
However, in its simplest form, this methodology can greatly benefit those tracking and identifying online criminals too. Being aware of what it is and how it works can aid anyone trying to identify a network of criminals. How do you think the EFCC in Nigeria is doubling their arrests and convictions a year? Because it works!
Local Police SNA Case Study
In January 2008 a collaborative pilot project was launched to explore the viability of incorporating SNA into the precinct-level crime analysis methodologies of the Richmond, Virginia, Police Department (RPD). Participants included representatives of RPD, a university sociologist, and a software designer. The goal was for the research team, comprised of the sociologist and the software designer, to use crime data to assess how constructive SNA would be in solving the most prevalent crimes in the area and to determine the feasibility of training the precinct-level analysts to incorporate it into their workflow.
Researchers needed to determine what initiated violence between two groups of previously friendly young males. Several persons of interest, at one time on good terms, began to argue and assault one another. The source of the violence was not clear, and police were looking for ways to respond. They wanted to know if SNA could help them understand what sparked the violence and which strategies could be developed using a network approach.
The research team received access to RPD’s records management system to obtain information on criminal occurrences, arrests, criminal associates, demographics, and victim/offender relationships. The police provided no other background information on the individuals. The research team did not meet or discuss the ongoing investigation with the detectives. Analysis was done off-site, and the only recurring contact was with the police manager to extract the data in relational form.
Using 24 persons of interest labeled by a gang unit detective as “seeds”—starting points, or initially identified persons—the records management system extracted all connections among the seeds from 2007 through October 2008, proceeding four layers out and including any interconnections among the seed and nodes in each step. The connections were categorized by incident type—common incident participation, victim/offender, gang memberships, field contacts, involved others, common locations, and positive or negative connections.
Positive ties included a cooperative relationship between individuals, such as having family connections, robbing a store together, or hanging out. Negative ties indicated hostile relationships, such as those between a victim and offender. Individuals could have multiple and varying connections. Four networks resulted from the sampling, one for each layer out from the seeds. The networks included the seeds, the relationships among them, people directly connected to them, and those related to their associates. This involved 434 individuals and 1,711 ties. Several weak spots existed where a single node connected regions of the network and indicated dense areas of heavy interconnectivity.
Using SNA software, an analyst quickly produced a visual representation, including names, to assess the structure of the group or reference to whom a person of interest was connected. Through visual analysis and examination of the metric of betweenness, analysts located the source of the disagreement. The metric pointed to critical junctures in the network that revealed interpersonal tensions among males revolving around their relationships with females.
Two powerful male gang members reportedly had a positive relationship in October of 2007; however, in April 2008, one victimized a female friend of the other. During the same incident, this male also victimized the female friend of another male. Throughout the episode, a pattern emerged involving situations where a dominant male engaged with a female associate of another strong male. In other words, boys were fighting over girls.
Quantitative metrics provided additional information identifying the powerful players in this network. By rank ordering the individuals according to their centrality measures, the analysis confirmed that the gang unit was watching the right people and using community resources effectively. The metrics also helped unit members further analyze the importance of the seed nodes. Many of the nodes targeted by the unit ranked as powerful in the network based on an SNA metric. The quantitative metrics indicated six other vital players, including one critical to the flow of the network.
Results
Unanticipated administrative processes delayed the timeline of the pilot project, making these results and recommendations too late to be actionable. The police already had solved the conflict. The knowledge of the detectives, which the research team was not privy to, validated the results. Officers confirmed that the answer the research team had discerned from the data—boys fighting over girls—was the cause of the conflict.
Detectives acknowledged that they would have solved the case more quickly and easily if they had this analysis available to guide their strategies. This feedback validated the worth of the approach and the usefulness of SNA and moved the project into the next phase. Precinct-level crime analysts received training in SNA through a 36-hour, in-house seminar. Through lectures and hands-on training, crime analysts from police and federal agencies used data from their own projects to learn to incorporate SNA to meet their needs. Within 2 weeks of completing the course, the analysts used SNA in several cases, including an aggravated assault/ shooting and several convenience store robberies.
In the shooting incident, the analyst used SNA to provide data on an associate of the suspect who previously was not noticed by the detective working the case. The analyst provided that information to the detective who used it to locate and interview that individual, which put additional pressure on the suspect, who was attempting to elude capture. This, combined with other social and financial pressures, caused the suspect to surrender.
Another case involved a string of convenience store robberies. Using an SNA map of a separate case, an analyst noticed a connection between a person of interest in the robberies in one precinct and a member of the network under investigation. Using the two names as seeds, the analyst extracted another previously unknown network. The analyst and a colleague identified one of the seed names as a person of interest in robberies involving multiple juveniles. Through cooperation and an SNA social diagram, they pieced together robberies not previously thought to be connected and identified a suspect involved in other robberies. The chart provided a source where they quickly, easily, and effectively could share observations with investigative personnel.
Social Network Diagrams
Social network diagrams have become a method for RPD to use social relationships among offenders and their associates. Renowned for its technological innovation and policing strategies, RPD has found SNA effective in facilitating better communication between crime analysts and investigators. SNA enabled the department to significantly increase crime clearance rates and reduce violence.
Prior to the SNA training, analysts conceptualized a series of “star” networks with an “ego” at the center and immediate connections radiating out. To understand the network, analysts identified the immediate connections of a person of interest. To identify one of the people connected to the original person of interest, a second ego network was constructed. In the end, the analyst faced a series of networks, leaving out the interconnections between them. Through training, analysts began to interpret the effectiveness of the larger network environment using diagrams as social maps to orient themselves and officers.
In the shooting case, the detective used the network analysis to apply pressure to the suspect by interviewing an associate whose relationship with the offender previously was unknown. Mounting social and financial pressures, ultimately, led the individual to surrender. In the convenience store robberies, an SNA diagram provided vital clues that allowed multiple analysts to share information and identify previously unknown connections between individuals, which led to a possible suspect. If SNA had been available to analysts in other jurisdictions, a connection may have been discovered earlier.
Analysis
The cases described illustrate the success of SNA in developing law enforcement strategies and interdiction techniques. The pilot project demonstrated how SNA can help answer sophisticated questions regarding motivations for a crime—an area previously underdeveloped in crime analysis processes. The research team was asked to determine why violence occurred among groups who previously were amicable. Using visual analysis and without any subject matter knowledge, investigators used SNA to reveal behavioral motivation rooted in complex interpersonal relationships. The project provided confirmation of the effectiveness of the current resource allocation of the gang unit and indicated new avenues of policing, which have the potential to produce a high return on investment.
These two cases produced actionable results, illustrating how SNA can facilitate a productive working relationship between crime analysts and detectives. The academic research on policing indicated that one of the biggest hurdles in establishing effective communication is finding a common language between the analytics of numbers and the immediate pressures of reality.4 Each case described illustrates how SNA and social network diagrams function as a common ground. Analysts used the charts visually to depict their analysis, which resonated with detectives because it reflected their reality. The analysts provided something new to the detectives, thus, aiding each investigation.
The visual and quantitative output of SNA helps solve institutional memory issues associated with analysts’ longevity and attrition, as well as new hires. By producing a current overview, SNA allows new analysts to grasp the present status of the network. It assists experienced analysts in maintaining an understanding of the network by chronicling growth and development as members and connections appear and disappear.
Law enforcement agencies, such as RPD, benefit from having access to structured, relational, and temporal data. Analysts reliably map changes in the network using an automated extraction process. Through this dynamic procedure, experienced analysts appear less likely to develop data analysis blind spots.
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Scott V. on The Persistence of Danielle Delaunay as a Fake Identity – 2026: “That was the woman they used with me!! They were able to send a video of her talking on one…” Jun 2, 16:02
- on The Persistence of Danielle Delaunay as a Fake Identity – 2026: “That’s sad but they do a lot” Jun 2, 14:39
- on Major General William Burke Garrett III – Another Stolen Identity Used To Scam Women: “I am from Guatemala. I was contacted by William Barret two weeks ago, who mentioned that he was a widower…” May 21, 17:13
- on Scam Grooming: Finding Common Interests: “I’ve been groomed for two months then the love bombing started. This guy was supposedly a Ukrainian soldier stationed in…” May 8, 13:56
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I was just very numb after my scam, I barely slept and was exhausted. I wish I had know about…” May 7, 22:31
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “I can barely handle myself these days so even thinking about another relationship is too much for me. The time…” May 7, 20:59
- on Revictimization – A High Risk for Existing Scam Victims – 2026: “Thank you! I understand that these impulse reactions can affect us for some time. And another relationship especially soon after…” May 7, 18:14
- on Reporting Scams To The United States Secret Service – Cryptocurrency Recovery – Forget The FBI! [VIDEO]: “Unfortunately, the Federal services tend to aggregate crimes together rather than investigate individual offenses when it comes to scams.” May 6, 01:57
- on Romance Scams Detection Training Tool – 2026: “Criminals are not toys, and they can harm you in ways you can’t even imagine.” May 6, 01:55
- on Romance Scams Detection Training Tool – 2026: “Great, word, by word as it is happening to me right now however I already stated clearly that I have…” May 2, 20:06
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.












Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.