
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years

SCARS™ Guide: There Is A New Kind Of Phishing Called Whaling Scam Attacks
Whaling: How It Works, And What Your Organisation Can Do About It
A GUIDE TO ‘WHALING’ – TARGETED PHISHING ATTACKS AIMED AT SENIOR EXECUTIVES
Whaling is a highly targeted phishing attack – aimed at senior executives – masquerading as a legitimate email. Whaling is digitally enabled fraud through social engineering, designed to encourage victims to perform a secondary action, such as initiating a wire transfer of funds.
Whaling does not require extensive technical knowledge yet can deliver huge returns. As such, it is one of the biggest risks facing businesses. Financial institutions and payment services are the most targeted organizations, however, cloud storage and file hosting sites, online services, and e-commerce sites are receiving a larger share of attacks.
Whaling emails are more sophisticated than generic phishing emails as they often target chief (‘c-level’) executives and usually:
- Contain personalized information about the targeted organization or individual
- Convey a sense of urgency
- Are crafted with a solid understanding of business language and tone
What Are The Consequences Of Whaling?
Whaling emails are a form of social engineering which aims to encourage their victim to take a secondary action such as:
- Clicking on a link to a site which delivers malware
- Requesting a transfer of funds to the attacker’s bank account
- Requests for additional details about the business or individual in order to conduct further attacks
Financial loss
The 2016 Phishing Trends and Intelligence report by PhishLabs™ found that 22% of spearphishing attacks analyzed in 2015 were motivated by financial fraud or related crimes. The table below illustrates five of the largest financial losses to organizations as a result of whaling emails. In these examples, a senior executive received a fraudulent email requesting a transfer of funds, from what appeared to be a trusted supplier, partner or member of the organization.
Clicking on a link or downloading an attachment in an email can result in corporate networks becoming infected with malware. This can result in data breaches such as the loss of customer data or intellectual property theft.
Reputational Damage From Whaling
Financial or data loss through a whaling attack can be extremely embarrassing to both an organization and an individual. FACC, an Austrian aerospace manufacturer that lost €50 million UK Pounds as a result of a targeted email attack in 2016, decided to fire several members of staff including the CEO, for their involvement in the incident.
Recent Changes In Common Whaling Tactics
Initially, whaling emails were not much harder to identify than their less targeted phishing counterparts. However, the adoption of fluent business terminology, industry knowledge, personal references, and spoofed email addresses have made sophisticated whaling emails difficult for even a cautious eye to identify. Highly targeted content is now combined with several other methods that executives should be aware of to reduce their chances of falling victim to a whaling attack. Crucially all these developments either exploit existing trusted relationships or combine a cyber-attack with non-cyber fraud tactics.
Whaling Email Followed Up With A Phone Call
The NCSC is aware of several incidents whereby a whaling email was received and then followed-up with a phone call confirming the email request.
This is a social engineering tactic that could be described as cyber-enabled fraud. The phone call serves the dual purpose of corroborating the email request and making the victim complacent about a possible cyberattack as they have also had a ‘real world’ interaction.
Whaling email from malicious actors masquerading as a trusted partner!
The rise of supply chain attacks (where a supplier or partner organization’s network is compromised in order to gain access to the target organization) has been well documented. However, recent whaling attacks have used easily accessible information on suppliers or partners to construct whaling emails that appear credible.
If an organization advertises partners such as charities, law firms, think tanks or academic institutions, they should be aware that they may receive emails from malicious actors masquerading as those trusted partners.
Whaling emails that appear to be from colleagues!
This is when an employee email address is either compromised (or a spoofed email address is used) to convince other employees that they are receiving a legitimate request from a colleague.
This is especially effective when the email address of a very senior executive is spoofed to request an urgent payment to a junior member of (for example) a finance department.
Whaling Through Social Media
Online social networking is an increasingly prevalent way of developing business contacts, recruiting employees and hosting discussions. However social media accounts, both professional and personal, provide a means for malicious actors to research and make contact with senior executives. They provide a goldmine of information for social engineering, and victims are often less vigilant to attack in a more social forum. According to Proof Point, there was a 150% increase in social media phishing attacks in 2015 (more recent data is not yet available).
Catching Your White Whale
It is crucial to remember that whaling is a means of social engineering, and malicious actors will use methods exploiting established trust structures, existing outside the cyber-realm, to reassure the victim.
Simply making your employees aware of social engineering threats doesn’t make them invulnerable; some attacks are too well crafted and no amount of user awareness and training can guarantee their detection. Employee and executive training on social engineering tactics should be considered part of a series of technical and user-based defenses against attacks, but recognize the limitations of such measures.
Similarly, whilst organizations should ensure training is supported by hardened technical defenses, malicious actors are increasingly employing techniques to evade automated detection and prevent analysis of attack methodology. As such, organizations should accept that a successful whaling attack is a possibility, and put in place checks and processes to mitigate the damage.
Whaling Examples
The following real-life whaling attempts show the intricate changes perpetrators try to make to trick a CEO.
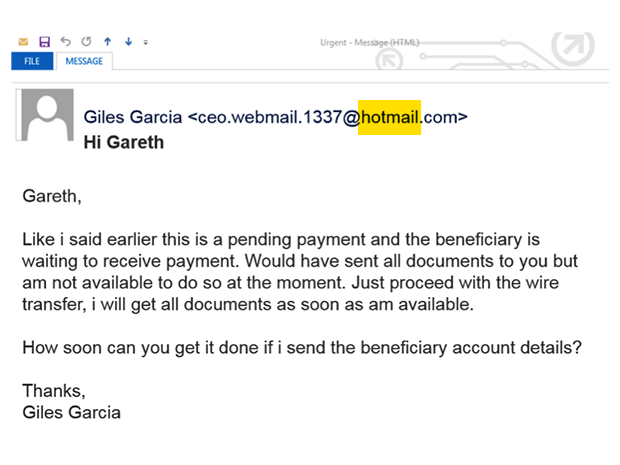
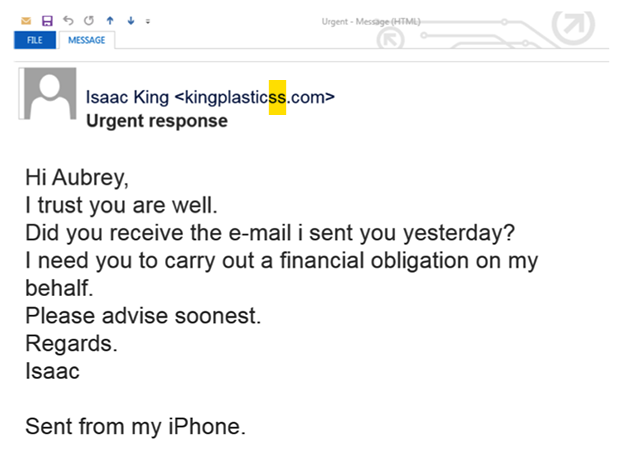
Whaling attempt where the attacker has created a Hotmail account that could appear to be a CEO webmail service. Source: NCSC.GOV.UK
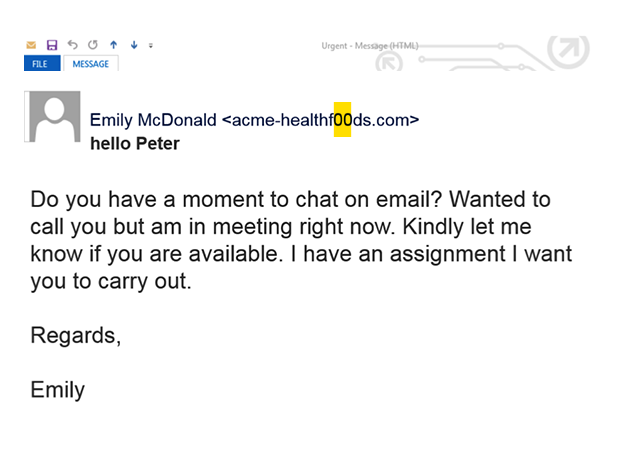
Whaling attempt where the attacker has registered a similar domain name, replacing the “o’s” with similar and easily overlooked zeros. Source: NCSC.GOV.UK
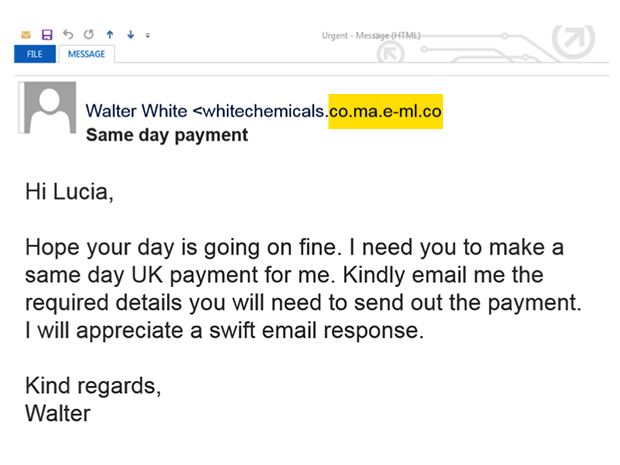
Whaling attempt where the attacker has registered a similar-looking domain name to the actual White Chemicals. Source: NCSC.GOV.UK
If your organization is looking for help to properly train your staff on Whaling and Social Engineering threats look no further than SCARS! One of the SCARS divisions specializes in providing business support for scams. Please visit www.USGCP.com » for more information.
Remember
Whaling, Spearphishing, and Phishing all depend on a willing victim to allow them to succeed!
Only by training and behavioral change can you defend against social engineering attacks – this is true for enterprises and consumers alike!
PLEASE SHARE OUR ARTICLES WITH YOUR CONTACTS
HELP OTHERS STAY SAFE ONLINE
SCARS™ Team
A SCARS Division
Miami Florida U.S.A.
TAGS: SCARS, Important Article, Information About Scams, Anti-Scam, Whaling Scam Attacks, Spearphishing Attacks, Phishing Scams, Corporate Penetration Attacks Via Email, Social Engineering Attacks
The Latest SCARS|RSN Posts
FIND MORE SCAM NEWS
«SCAMCRIME.COM»
CHAT WITH SCARS™
«CLICK HERE»
END
MORE INFORMATION
– – –
Tell us about your experiences with Romance Scammers in our
« Scams Discussion Forum on Facebook »
– – –
FAQ: How Do You Properly Report Scammers?
It is essential that law enforcement knows about scams & scammers, even though there is nothing (in most cases) that they can do.
Always report scams involving money lost or where you received money to:
- Local Police – ask them to take an “informational” police report – say you need it for your insurance
- U.S. State Police (if you live in the U.S.) – they will take the matter more seriously and provide you with more help than local police
- Your National Police or FBI « www.IC3.gov »
- The SCARS|CDN™ Cybercriminal Data Network – Worldwide Reporting Network « HERE » or on « www.Anyscam.com »
This helps your government understand the problem, and allows law enforcement to add scammers on watch lists worldwide.
– – –
Visit our NEW Main SCARS Facebook page for much more information about scams and online crime: « www.facebook.com/SCARS.News.And.Information »
To learn more about SCARS visit « www.AgainstScams.org »
Please be sure to report all scammers
« HERE » or on « www.Anyscam.com »
Legal Notices:
All original content is Copyright © 1991 – 2020 SCARS All Rights Reserved Worldwide & Webwide. Third-party copyrights acknowledge.
SCARS, RSN, Romance Scams Now, SCARS|WORLDWIDE, SCARS|GLOBAL, SCARS, Society of Citizens Against Relationship Scams, Society of Citizens Against Romance Scams, SCARS|ANYSCAM, Project Anyscam, Anyscam, SCARS|GOFCH, GOFCH, SCARS|CHINA, SCARS|CDN, SCARS|UK, SCARS Cybercriminal Data Network, Cobalt Alert, Scam Victims Support Group, are all trademarks of Society of Citizens Against Relationship Scams Incorporated.
Contact the law firm for the Society of Citizens Against Relationship Scams Incorporated by email at legal@AgainstScams.org
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Debby Montgomery Johnson on The Danger of Using AI in Law Enforcement – The Grandmother Wrongly Arrested as a Fraudster – 2026: “Excellent article – I can’t imagine the terror Angela most certainly experienced. Compound this with the lack of accountability by…” Mar 24, 09:20
- on The Crazy Gregor MacGregor and the Country of Poyais Scam – History of Scams – 2026: “interesting” Mar 23, 19:24
- on BEC Fraud Reaches $43 Billion Per Year: “oh my gosh so much of an increase in the fraud I pray the officials can continue tracking and make…” Mar 23, 15:09
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Make Online Safe Again!” Mar 17, 19:11
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Finally an administration takes the initiative to help solve the gigantic situation. Make America Safe Again, thank you!” Mar 17, 15:41
- on What Is The Difference Between A Scam Victim And A Scam Survivor? [Updated]: “Due to my scams I don’t fully trust anyone online and I shouldn’t even those people I knew in high…” Mar 7, 12:46
- on SCARS 3 Steps For New Scam Victims 2024: “I was very fearful “he” would come to my home because I was knew my address, I spoke to someone…” Mar 7, 09:50
- on Sadness & Scam Recovery: “Before my scam, my mom passed away and I got a divorce, so I was dealing with the loss of…” Mar 7, 09:37
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is NO evidence and she is not, she is a victim too. Sebastian, stop letting your anger think for…” Mar 6, 23:18
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is real evidence that behind these two people there is something that not many people know. This woman is…” Mar 4, 03:58
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.























Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.