
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years

PDFs: The Most Underestimated Cyber Threat
When it comes to personal or business cybersecurity, the focus often falls on sophisticated malware and intricate hacking techniques. However, one usually overlooked vector for cyberattacks is the ubiquitous PDF (Portable Document Format) file.
PDFs are widely used for sharing documents, presentations, and other forms of content, but they can also be exploited by attackers to deliver malicious payloads and compromise unsuspecting users.
Can PDFs have viruses?
Yes, they can. Because PDFs are one of the most universally used file types, hackers and bad actors can find ways to use these normally harmless files — just like dot-com files, JPGs, Gmail, and Bitcoin — to create security threats via malicious code.
In A Hurry And Want To Check A File Now?
Scanning a PDF for viruses in a hurry: Many tools work equally well for Mac or PC users. One of the most popular is VirusTotal, which might be the best solution when you’re in a hurry because it doesn’t even require a download or software installation.
Go here to scan a saved PDF: VirusTotal File Scan
The Appeal of PDFs for Cyberattacks
There are several reasons why PDFs are attractive to cybercriminals:
-
Ubiquity: PDFs are widely used and supported across various operating systems and software applications, making them a convenient and accessible target for attackers.
-
Ease of Exploitation: Vulnerabilities in PDF readers and the format itself can be exploited to execute malicious code or embed hidden data within the document.
-
Undetectability: PDFs can be carefully crafted to bypass security measures and remain undetected by antivirus software and other security tools.
-
Social Engineering: Attackers can leverage social engineering tactics, such as phishing emails with attached PDFs, to trick users into opening infected documents.
PDF Attack Techniques
Attackers employ various techniques to exploit PDFs for cyberattacks, here are the most common ones:
-
Embedding Malicious Code: Attackers can embed malicious code, such as JavaScript or Flash, within PDFs to take control of a user’s system when the document is opened.
-
Exploiting Vulnerabilities: Attackers can exploit vulnerabilities in PDF readers or the format itself to execute arbitrary code on a user’s system.
-
Data Embedding: Attackers can embed hidden data, such as stolen credentials or sensitive information, within PDFs, making it difficult to detect and remove.
-
Phishing Attacks: Attackers can use PDFs as attachments in phishing emails to trick users into opening infected documents, allowing malware to be installed or sensitive information to be stolen.
An explanation of the different ways hackers can exploit PDFs to deliver malicious payloads and compromise users:
Malicious Attachments:
Hackers can attach files like executables or scripts to PDFs. When you open the PDF, these attachments can run automatically, installing malware on your computer.
Embedded Links:
PDFs can contain links that, when clicked, take you to malicious websites. These websites can contain malware, phishing pages, or exploit kits that target vulnerabilities in your system.
Exploiting PDF Vulnerabilities:
Hackers can take advantage of weaknesses in PDF software itself. If you open a PDF using an outdated PDF reader, the hacker can execute code that harms your system.
Hidden Content and Layers:
PDFs can have layers and hidden content. Hackers can hide malicious content behind seemingly harmless information. When opened, this hidden content can be revealed and perform malicious actions.
Malicious JavaScript:
PDFs can contain JavaScript code that runs when you open the PDF. Hackers can use JavaScript to download malware, steal your information, or redirect you to malicious websites.
Phishing Attacks:
Hackers can create PDFs that look like legitimate documents, such as invoices, contracts, or forms. These fake documents may contain links to phishing sites or ask for your personal information.
Malicious Macros:
Some PDF readers support macros, similar to those in Microsoft Office documents. Hackers can embed malicious macros in PDFs that, when enabled, can execute code leading to malware infection.
Document Exploitation:
Hackers can embed exploits within PDF files that target software vulnerabilities. These vulnerabilities could allow the hacker to take control of your system.
Watering Hole Attacks:
In a watering hole attack, hackers compromise a website you frequently visit. They then inject malicious code into a PDF hosted on the compromised site. When you download and open the PDF, your system could be compromised.
Document Encryption and Passwords:
Some hackers send password-protected PDFs via email, claiming the password is provided in the message. In your haste, you might enter the password, allowing the hacker to access your system or sensitive information.
NOTE: Just because a PDF may have a password does not mean it is safe!
Take These Precautions Against PDF-Based Attacks
Determining the safety of a PDF file before opening it is crucial to protect yourself from potential cyberattacks. Here are some effective strategies to verify the safety of a PDF:
- Browser PDF reader extension: make sure it is a reputable extension from a trusted maker.
- Browser Anti-Malware extension installed: Such as MalwareBytes or Bitdefender.
- Adobe brand is the official PDF reader: install the Adobe PDF reader for safety.
-
Check the Sender’s Origin: If you receive a PDF via email, carefully examine the sender’s email address. If it appears unfamiliar, suspicious, or from an unknown source, exercise caution and avoid opening the attachment. NOTE: this is no guaranty, it could have come from someone you know and their computer was compromised.
-
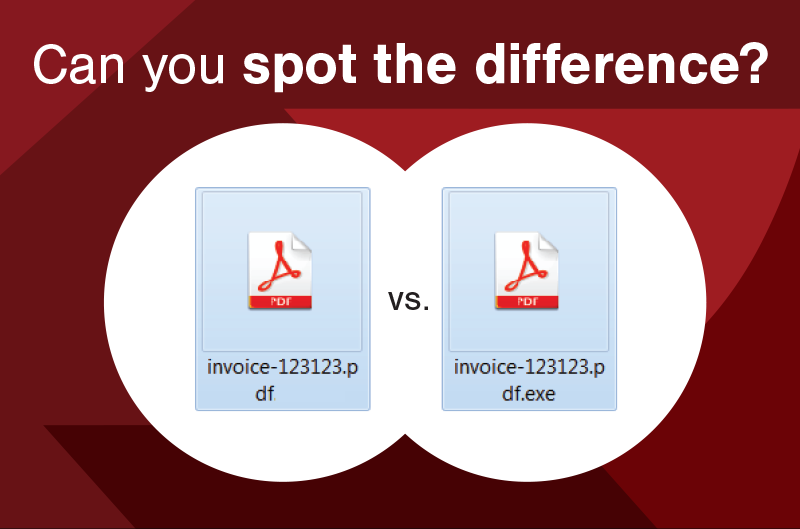
Verify the File Extension: Ensure that the file extension is indeed .pdf and not .exe or another executable format. Malicious actors often disguise malware as PDFs by changing the extension.
-
Scan the PDF with Antivirus/Anti-Malware Software: Utilize a reputable antivirus software to scan the PDF before opening it. This can help detect and remove embedded malware or potential threats. SCARS uses MalwareBytes
-
Enable Protected View: Most PDF readers offer a “Protected View” mode that restricts the execution of potentially harmful code within the PDF. Enable this mode to add an extra layer of protection.
-
Hover over Links: Before clicking on any links within the PDF, hover your cursor over them to reveal the actual destination URL. If the URL appears suspicious or unfamiliar, avoid clicking on it.
-
Check for Embedded Macros: Some PDF readers support macros, which can be used to automate tasks or execute code. If the PDF contains macros, proceed with caution and only enable them if you trust the source.
-
Avoid Opening PDFs from Untrusted Sources: Refrain from opening PDFs attached to unsolicited emails or downloaded from untrusted websites. These sources are more likely to contain malicious PDFs.
-
Update PDF Reader Software: Keep your PDF reader software up to date to ensure it has the latest security patches and vulnerability fixes.
-
Educate Yourself: Stay informed about the latest PDF-based attack techniques and educate yourself on how to identify and avoid them.
By following these precautions, you can significantly reduce the risk of opening a malicious PDF and compromising your device or sensitive information. Remember, vigilance and awareness are key to staying safe in the digital world.
Summary
PDFs, while essential for document sharing and collaboration, can also pose a significant cybersecurity threat. By understanding the risks associated with PDFs and taking appropriate precautions, users can protect themselves from malicious actors and safeguard their valuable information. Remember, vigilance and awareness are key to staying safe in the ever-evolving cybersecurity landscape.
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Wendy Guiher on 15 Things That Nearly Every Online and Phone Scams Have In Common – 2026: “Very concise, direct information. When I look back on the crime against me I now can see ALL of the…” Apr 1, 06:24
- on The Danger of Using AI in Law Enforcement – The Grandmother Wrongly Arrested as a Fraudster – 2026: “Excellent article – I can’t imagine the terror Angela most certainly experienced. Compound this with the lack of accountability by…” Mar 24, 09:20
- on The Crazy Gregor MacGregor and the Country of Poyais Scam – History of Scams – 2026: “interesting” Mar 23, 19:24
- on BEC Fraud Reaches $43 Billion Per Year: “oh my gosh so much of an increase in the fraud I pray the officials can continue tracking and make…” Mar 23, 15:09
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Make Online Safe Again!” Mar 17, 19:11
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Finally an administration takes the initiative to help solve the gigantic situation. Make America Safe Again, thank you!” Mar 17, 15:41
- on What Is The Difference Between A Scam Victim And A Scam Survivor? [Updated]: “Due to my scams I don’t fully trust anyone online and I shouldn’t even those people I knew in high…” Mar 7, 12:46
- on SCARS 3 Steps For New Scam Victims 2024: “I was very fearful “he” would come to my home because I was knew my address, I spoke to someone…” Mar 7, 09:50
- on Sadness & Scam Recovery: “Before my scam, my mom passed away and I got a divorce, so I was dealing with the loss of…” Mar 7, 09:37
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is NO evidence and she is not, she is a victim too. Sebastian, stop letting your anger think for…” Mar 6, 23:18
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.















Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.