
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years


DMV Vehicle Registration Cancellation Text Scam
How Criminals Use Fake DMV Messages to Steal Personal and Financial Information
A New Wave of Urgent Text Message Scams
How Scams Work / Catalog of Scams – A SCARS Institute Insight
Article Abstract
Criminal networks are distributing large-scale text message phishing campaigns across the United States that falsely claim a recipient’s vehicle registration has been cancelled by a state Department of Motor Vehicles. The messages create urgency by warning of fines, driving restrictions, or legal consequences and direct recipients to a link that appears to resolve the issue. The links lead to fraudulent websites designed to collect personal information, identity data, or payment for fake reinstatement fees. The scheme relies on mass SMS distribution, domain name manipulation that mimics government websites, and psychological pressure involving authority, fear, and short deadlines. Investigations indicate that organized cybercrime groups operate these campaigns using automated messaging systems and phishing infrastructure, allowing millions of messages to be distributed. Public awareness and independent verification through official government websites remain critical defenses against these scams.

Vehicle Registration Cancellation Text Scam: How Criminals Use Fake DMV Messages to Steal Personal and Financial Information
A New Wave of Urgent Text Message Scams
Across the United States, criminals are launching a rapidly growing phishing scheme through text messages that falsely claim a person’s vehicle registration has been cancelled. These messages are designed to create fear and urgency. They warn about driving restrictions, fines, legal penalties, or immediate enforcement actions if the recipient does not act quickly.
The message usually appears to come from a state Department of Motor Vehicles or another official government authority. It often includes a deadline of only one or two days and provides a link that supposedly allows the recipient to “resolve the issue immediately.”
In reality, the message is part of a coordinated phishing campaign operated by organized cybercriminal groups. The goal is to trick recipients into clicking a malicious link and providing personal information, payment details, or both.
This scam illustrates a broader shift in cyber-enabled fraud. Criminals increasingly exploit everyday administrative systems such as vehicle registration, toll payments, tax notices, and package deliveries because these topics feel routine and believable. The strategy relies on psychological pressure rather than technical sophistication.
Understanding how this scam works helps individuals recognize the warning signs and protect themselves from becoming victims.
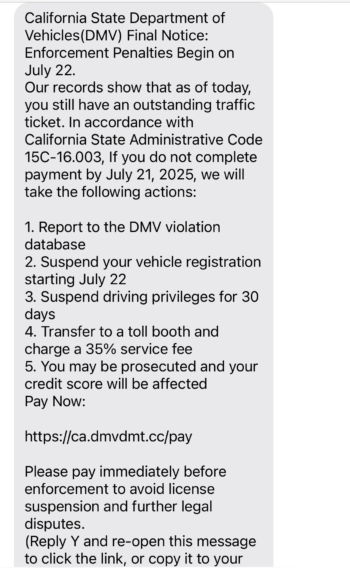
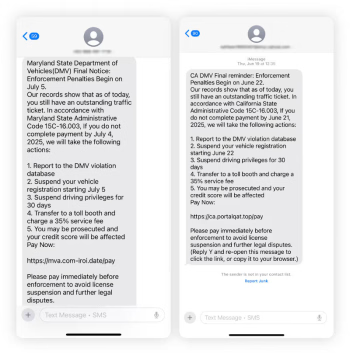
What the Message Usually Looks Like
The scam begins with a text message that appears official and authoritative. The wording varies slightly, but the structure remains consistent.
The message typically claims that the recipient’s vehicle registration has been cancelled, suspended, or flagged due to an administrative issue. It may warn that driving privileges could be restricted or that penalties will apply if the matter is not resolved quickly.
Common elements include:
- A reference to a state DMV or motor vehicle authority
- A statement that the vehicle registration is cancelled or suspended
- Threats of fines, penalties, or enforcement actions
- A short deadline, often 24 to 48 hours
- A link that claims to allow immediate resolution
The link often appears legitimate at first glance. It may contain words such as “dmv,” “vehicle,” “registration,” or the name of a state. The link structure is deliberately designed to mimic real government websites.
However, these links lead to fraudulent websites controlled by scammers.
How the Scam Works Step by Step
Step 1: Mass Text Distribution
The scam begins with automated systems that send thousands or even millions of text messages simultaneously. Criminal groups use specialized messaging platforms that allow bulk distribution of SMS messages at extremely low cost.
Phone numbers are obtained from data breaches, leaked databases, purchased marketing lists, or automated number-generation tools.
Because the messages are sent to large numbers of people, criminals do not need to know whether the recipient actually owns a vehicle. Statistical probability ensures that many recipients will.
Step 2: Creating Urgency and Fear
The message is designed to trigger immediate emotional reactions. Fear and urgency reduce the likelihood that a person will pause and verify the information.
Statements about cancelled registrations, fines, or legal consequences create pressure to act quickly. The short deadline increases anxiety and discourages careful thinking.
This technique is a classic example of psychological manipulation used in phishing and social engineering.
Step 3: Redirecting to a Fake Website
When the recipient clicks the link, they are directed to a fraudulent website that closely resembles an official DMV site.
These websites often include:
- State logos or government-style graphics
- Official-sounding language
- Forms requesting personal information
- Payment portals requesting fees or penalties
The site may claim that a registration fee or reinstatement penalty must be paid to restore the vehicle’s legal status.
Step 4: Harvesting Personal Information
The fake site may ask for sensitive information such as:
- Full name
- Address
- Driver’s license number
- Vehicle identification number
- Date of birth
- Social Security number
Even if no payment is requested, the collection of personal data allows criminals to commit identity theft or sell the information on criminal marketplaces.
Step 5: Collecting Fraudulent Payments
Many versions of the scam request immediate payment of a small “reinstatement fee.” This amount may range from $25 to several hundred dollars.
Payments may be requested through credit cards, debit cards, or digital payment platforms.
Once the payment is made, the funds are quickly transferred through multiple accounts and often routed overseas. This makes recovery extremely difficult.
The Subtle Website Trick That Makes the Scam Look Real
One of the most effective tactics used in this scam involves manipulating website addresses to look legitimate.
Criminals often create domain names that contain official-looking words combined with subtle alterations.
Examples may include:
- Additional words inserted into the domain name
- Misspellings that are easy to overlook
- Extra characters or hyphens
- Domains ending in unfamiliar extensions instead of “.gov”
For example, a fraudulent link might include the word “dmv” or a state abbreviation but actually lead to a privately registered domain.
Many people glance at the beginning of a link without examining the full address. Scammers exploit this behavior by designing domains that appear official at first glance.
Because government agencies in the United States generally use “.gov” domains, any DMV link that does not end in “.gov” should be treated with suspicion.
Who Is Behind These Scams
These scams are rarely the work of individual criminals acting alone. They are typically conducted by organized cybercrime groups that operate internationally.
Many of these networks function as professional fraud operations. They use specialized tools, data brokers, automated messaging systems, and payment-laundering channels.
Investigations by law enforcement agencies and cybersecurity researchers have linked similar phishing campaigns to transnational criminal organizations operating in multiple regions.
These groups often maintain large infrastructures that include:
- phishing website generators
- automated SMS distribution systems
- stolen identity databases
- money-laundering networks
Some groups operate in regions where law enforcement cooperation is limited, making prosecution extremely difficult.
The Magnitude of the Problem
Text-based phishing, often called “smishing,” has grown dramatically in recent years.
Cybercriminals increasingly favor SMS messages because they bypass many traditional email security systems and reach people directly on their mobile devices.
Several factors contribute to the rapid growth of these scams:
- First, text messages carry a sense of personal urgency. Many people assume that messages sent to their phones are more trustworthy than emails.
- Second, smartphones make it easy to click links instantly without inspecting them carefully.
- Third, criminals can send millions of messages at extremely low cost.
Government impersonation scams have become especially common because they leverage authority and fear. Messages claiming to come from tax agencies, toll authorities, and motor vehicle departments are particularly effective.
Reports to federal and state agencies show that impersonation scams are among the fastest-growing categories of cyber-enabled fraud.
Why These Scams Are So Effective
Several psychological factors explain why many people respond to these messages.
Authority
The message appears to come from a government agency. Authority increases perceived legitimacy and reduces skepticism.
Urgency
Short deadlines create pressure and discourage careful verification.
Fear of Consequences
Warnings about fines, driving restrictions, or legal penalties trigger anxiety and a desire to resolve the problem immediately.
Routine Plausibility
Vehicle registration is a normal administrative responsibility. The message, therefore, feels believable.
These elements combine to create a powerful manipulation strategy.
Warning Signs That Reveal the Scam
Although the messages are designed to appear legitimate, several warning signs usually reveal the fraud.
- Government agencies rarely initiate enforcement actions through text messages.
- Official notices about vehicle registration are typically delivered through mail or secure online accounts.
- Urgent threats demanding immediate action are a common tactic used in scams.
- Links that do not end in “.gov” should be treated as suspicious when they claim to represent government agencies.
- Poor grammar, unusual formatting, or unfamiliar web addresses are also common indicators.
Recognizing these signs can prevent victims from engaging with the scam.
What Individuals Should Do If They Receive the Message
Anyone who receives a suspicious message about vehicle registration should take several steps.
- First, do not click the link in the message.
- Second, do not respond to the text or provide personal information.
- Third, verify the information independently by visiting the official DMV website for the state in question. This should be done by manually typing the address into a browser rather than following a link.
- Fourth, report the message to appropriate authorities or consumer protection agencies.
Blocking the sender can also reduce the likelihood of receiving additional scam messages.
Recovery Steps If Someone Clicked the Link
- If a person has already interacted with the scam website, several protective actions may help reduce the risk of further harm.
- If payment information was entered, the individual should contact the financial institution immediately and report the fraudulent transaction.
- If personal identification information was provided, monitoring credit reports and placing fraud alerts may help detect identity theft.
Passwords associated with the affected accounts should be changed immediately.
Reporting the incident to law enforcement and fraud reporting centers can also support investigations and prevention efforts.
Why Digital Safety Is Now a Life Skill
Scams delivered through text messages illustrate how fraud has become embedded in everyday digital communication.
Criminals now exploit routine activities such as receiving packages, paying tolls, renewing registrations, and filing taxes. These activities provide realistic scenarios that scammers can imitate.
Because of this shift, digital safety has become an essential life skill. Recognizing manipulation tactics, verifying official communications, and approaching urgent digital messages with caution are now basic protective behaviors.
Public awareness plays a critical role in preventing these scams. The more people understand how these schemes operate, the less effective they become.
Conclusion
The vehicle registration cancellation text scam demonstrates how modern fraud blends psychological manipulation with digital technology. By impersonating government agencies and creating urgency, criminals attempt to pressure individuals into revealing personal information or sending money.
These scams are typically operated by organized cybercrime networks that distribute messages on a massive scale. Their success relies on speed, emotional pressure, and the appearance of official authority.
Recognizing the warning signs, avoiding suspicious links, and verifying information through official sources can prevent individuals from becoming victims.
As digital communication continues to evolve, understanding these tactics becomes increasingly important. Awareness, caution, and verification remain the strongest defenses against scams that arrive unexpectedly on a smartphone screen.

Glossary
- Administrative Issue Claim — In this scam, criminals falsely claim that a vehicle registration has been cancelled, suspended, or flagged because of an administrative problem. The statement creates concern that a legal requirement has not been met and pressures the recipient to act immediately without verifying the claim through official channels.
- Automated Number Generation — Criminal networks often use software tools that generate large numbers of potential phone numbers automatically. These systems allow scammers to distribute messages broadly without knowing whether the recipients actually own vehicles or have DMV accounts.
- Automated SMS Distribution System — Organized fraud groups frequently operate software platforms capable of sending millions of text messages simultaneously. These systems allow scammers to conduct large-scale phishing campaigns quickly and cheaply while concealing the identity and location of the operators.
- Bulk Messaging Platform — A bulk messaging platform is a technology service that allows large volumes of text messages to be sent to thousands or millions of recipients at once. Cybercriminal groups exploit these systems to distribute fraudulent messages widely with minimal cost or technical effort.
- Click Trigger Behavior — Click trigger behavior describes the psychological impulse to immediately click a link in response to an alarming or urgent message. Scammers design messages to activate this reaction before a person has time to evaluate whether the message is legitimate.
- Coordinated Phishing Campaign — A coordinated phishing campaign refers to a structured operation in which criminal groups send large numbers of deceptive messages designed to obtain personal information or payments. These campaigns are typically organized with infrastructure, scripts, and automated tools that allow the scheme to operate at a massive scale.
- Credit Monitoring Response — Credit monitoring response refers to the protective action taken after personal information may have been exposed to criminals. Monitoring credit reports helps detect identity theft early and allows victims to respond quickly if fraudulent accounts are opened.
- Cyber Enabled Fraud — Cyber-enabled fraud refers to criminal activity that relies on digital technologies such as text messaging, websites, and online payment systems to deceive victims and obtain money or personal data.
- Cybercrime Infrastructure — Cybercrime infrastructure refers to the systems, tools, and digital resources that criminal organizations use to carry out online fraud. These may include messaging software, phishing website generators, stolen identity databases, and payment laundering networks.
- Data Breach Phone List — Data breach phone lists consist of phone numbers obtained from previously compromised databases. Criminal groups use these lists to send scam messages to individuals whose information was exposed in earlier cyber incidents.
- Deadline Pressure Messaging — Deadline pressure messaging is a manipulation technique in which scammers impose a short response window such as 24 or 48 hours. The artificial deadline increases anxiety and encourages rapid decisions without verification.
- Department of Motor Vehicles Impersonation — Department of Motor Vehicles impersonation occurs when criminals falsely present themselves as representatives of a state motor vehicle authority. The tactic relies on the credibility of government agencies to make fraudulent messages appear legitimate.
- Digital Payment Request — A digital payment request in this scam typically appears as a reinstatement fee or penalty required to restore vehicle registration status. Victims who pay the fee unknowingly transfer money directly to criminal accounts.
- Domain Name Manipulation — Domain name manipulation refers to the practice of creating website addresses that resemble legitimate government or institutional domains. Scammers use minor spelling changes or extra words to make fraudulent sites appear authentic.
- Emotional Reaction Trigger — Emotional reaction triggers are phrases or warnings designed to provoke fear or anxiety. Messages about cancelled registrations, fines, or driving restrictions are used to provoke immediate concern that overrides careful thinking.
- Enforcement Threat Messaging — Enforcement threat messaging refers to statements warning about fines, legal penalties, or restrictions on driving privileges. These threats are intended to pressure recipients into responding quickly without checking whether the claim is legitimate.
- Fraudulent Payment Portal — A fraudulent payment portal is a fake online payment page designed to capture credit card or debit card information. These portals often mimic official government payment systems but transfer funds directly to criminal accounts.
- Fraudulent Reinstatement Fee — A fraudulent reinstatement fee is a payment demanded by scammers who claim that a vehicle registration must be restored after cancellation. The fee appears small enough to seem believable, but is entirely fabricated.
- Government Authority Appearance — Government authority appearance refers to visual and textual elements that make a message seem official. Scammers use formal language, government names, and administrative terminology to imitate legitimate communications.
- Government Domain Verification — Government domain verification refers to the practice of confirming that a website address ends in the official government domain extension used in the United States. This step helps individuals determine whether a site is legitimate or fraudulent.
- Government Impersonation Messaging — Government impersonation messaging is a deception strategy in which criminals pretend to represent a public agency. Messages that claim to come from motor vehicle departments, tax authorities, or toll agencies are common examples.
- Identity Theft Risk Exposure — Identity theft risk exposure occurs when victims unknowingly provide sensitive information to a fraudulent website. Personal identifiers such as driver’s license numbers and dates of birth may later be used to commit financial fraud.
- Immediate Resolution Link — An immediate resolution link is a hyperlink provided in the scam message that claims to allow the recipient to correct the alleged registration problem. In reality, the link redirects users to a fraudulent website controlled by criminals.
- Link Structure Mimicry — Link structure mimicry refers to the deliberate design of website addresses that resemble legitimate government websites. Criminals place familiar words such as DMV or vehicle registration at the beginning of the domain to mislead readers.
- Malicious Website Redirection — Malicious website redirection occurs when a victim clicks a link in a scam message and is automatically sent to a fraudulent website. The page often imitates official government portals to increase the illusion of legitimacy.
- Mass Text Distribution — Mass text distribution is the large-scale sending of SMS messages to thousands or millions of recipients simultaneously. Criminal groups rely on this approach to increase the probability that some recipients will respond.
- Money Laundering Channel — Money laundering channels are financial pathways used by criminals to move stolen funds through multiple accounts or countries. These systems make it extremely difficult for investigators to trace or recover the stolen money.
- Motor Vehicle Authority Reference — Motor vehicle authority references in scam messages are used to create legitimacy by mentioning official agencies responsible for vehicle registration and licensing. The tactic exploits the public’s familiarity with these agencies.
- Organized Cybercrime Group — Organized cybercrime groups are structured criminal networks that specialize in online fraud. These groups often operate internationally and maintain dedicated tools, personnel, and infrastructure for large-scale scams.
- Payment Laundering Network — Payment laundering networks are systems used by criminals to move fraudulent payments through intermediaries and financial platforms. This process helps obscure the origin of stolen funds and protects the operators from detection.
- Personal Data Harvesting Form — Personal data harvesting forms are fields on fraudulent websites that request information such as addresses, identification numbers, and dates of birth. Victims may believe the information is required to resolve a legitimate problem.
- Phishing Website Generator — Phishing website generators are software tools that allow criminals to quickly create convincing copies of legitimate websites. These tools enable large numbers of fraudulent sites to be deployed during scam campaigns.
- Psychological Pressure Strategy — Psychological pressure strategy refers to the deliberate use of fear, urgency, and authority to influence behavior. Scammers rely on emotional reactions rather than technical hacking to persuade victims to cooperate.
- Routine Administrative Plausibility — Routine administrative plausibility describes how scammers exploit common bureaucratic processes such as vehicle registration renewals. Because these tasks are familiar, victims may assume the message is legitimate.
- Scam Message Formatting Pattern — Scam message formatting patterns include consistent structures used by criminals when composing fraudulent messages. These patterns often contain warnings, deadlines, and links intended to provoke quick responses.
- Secure Account Verification — Secure account verification refers to the process of independently checking an account status by visiting the official government website. This step allows individuals to confirm whether a message about vehicle registration is genuine.
- SMS Phishing Technique — SMS phishing technique refers to the use of text messages to deceive individuals into revealing personal or financial information. This method bypasses many email security systems and reaches people directly on their mobile phones.
- Social Engineering Manipulation — Social engineering manipulation involves influencing human behavior rather than exploiting technical vulnerabilities. Scammers rely on persuasion, authority, and urgency to encourage victims to reveal information voluntarily.
- Statistical Targeting Method — Statistical targeting methods involve sending fraudulent messages to extremely large audiences without verifying individual details. Criminals rely on probability to ensure that a portion of recipients will respond.
- Suspicious Web Address Indicator — Suspicious web address indicators include unusual spelling, unfamiliar domain endings, or extra characters in a website link. Recognizing these indicators helps individuals identify fraudulent sites before entering personal information.
- Text Message Impersonation Scheme — A text message impersonation scheme involves criminals sending messages that appear to come from legitimate organizations. The goal is to exploit trust in familiar institutions to obtain personal data or payments.
- Transnational Cybercrime Operation — Transnational cybercrime operations involve criminal organizations that operate across multiple countries. These groups coordinate fraud activities through international networks and often operate beyond the reach of local law enforcement.
- Vehicle Registration Cancellation Claim — A vehicle registration cancellation claim is the central false statement used in this scam. The message asserts that the recipient’s registration has been cancelled or suspended and must be corrected immediately.
- Vehicle Registration Reinstatement Page — A vehicle registration reinstatement page is a fraudulent webpage designed to resemble an official government service portal. The page requests identification details and payment for a fake administrative fee.
- Victim Verification Delay — Victim verification delay refers to the brief pause during which individuals check whether a message is legitimate. Scammers attempt to eliminate this delay by creating urgency and emotional pressure.
- Warning Sign Recognition — Warning sign recognition involves identifying common characteristics of scam communications, such as urgent threats, unfamiliar web addresses, and requests for personal data. Recognizing these indicators can prevent individuals from engaging with fraudulent messages.
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
Table of Contents
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Wendy Guiher on 15 Things That Nearly Every Online and Phone Scams Have In Common – 2026: “Very concise, direct information. When I look back on the crime against me I now can see ALL of the…” Apr 1, 06:24
- on The Danger of Using AI in Law Enforcement – The Grandmother Wrongly Arrested as a Fraudster – 2026: “Excellent article – I can’t imagine the terror Angela most certainly experienced. Compound this with the lack of accountability by…” Mar 24, 09:20
- on The Crazy Gregor MacGregor and the Country of Poyais Scam – History of Scams – 2026: “interesting” Mar 23, 19:24
- on BEC Fraud Reaches $43 Billion Per Year: “oh my gosh so much of an increase in the fraud I pray the officials can continue tracking and make…” Mar 23, 15:09
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Make Online Safe Again!” Mar 17, 19:11
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Finally an administration takes the initiative to help solve the gigantic situation. Make America Safe Again, thank you!” Mar 17, 15:41
- on What Is The Difference Between A Scam Victim And A Scam Survivor? [Updated]: “Due to my scams I don’t fully trust anyone online and I shouldn’t even those people I knew in high…” Mar 7, 12:46
- on SCARS 3 Steps For New Scam Victims 2024: “I was very fearful “he” would come to my home because I was knew my address, I spoke to someone…” Mar 7, 09:50
- on Sadness & Scam Recovery: “Before my scam, my mom passed away and I got a divorce, so I was dealing with the loss of…” Mar 7, 09:37
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is NO evidence and she is not, she is a victim too. Sebastian, stop letting your anger think for…” Mar 6, 23:18
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.















Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.