
SCARS Institute’s Encyclopedia of Scams™ Published Continuously for 25 Years


15 Things That Nearly Every Online and Phone Scams Have In Common
Things Almost All Online and Phone Scams Seem to Share
How Scams Work – A SCARS Institute Insight
Author:
• Tim McGuinness, Ph.D., DFin, MCPO, MAnth – Recoverologist, Anthropologist, Scientist, Director of the Society of Citizens Against Relationship Scams Inc.
See Author Biographies Below
Article Abstract
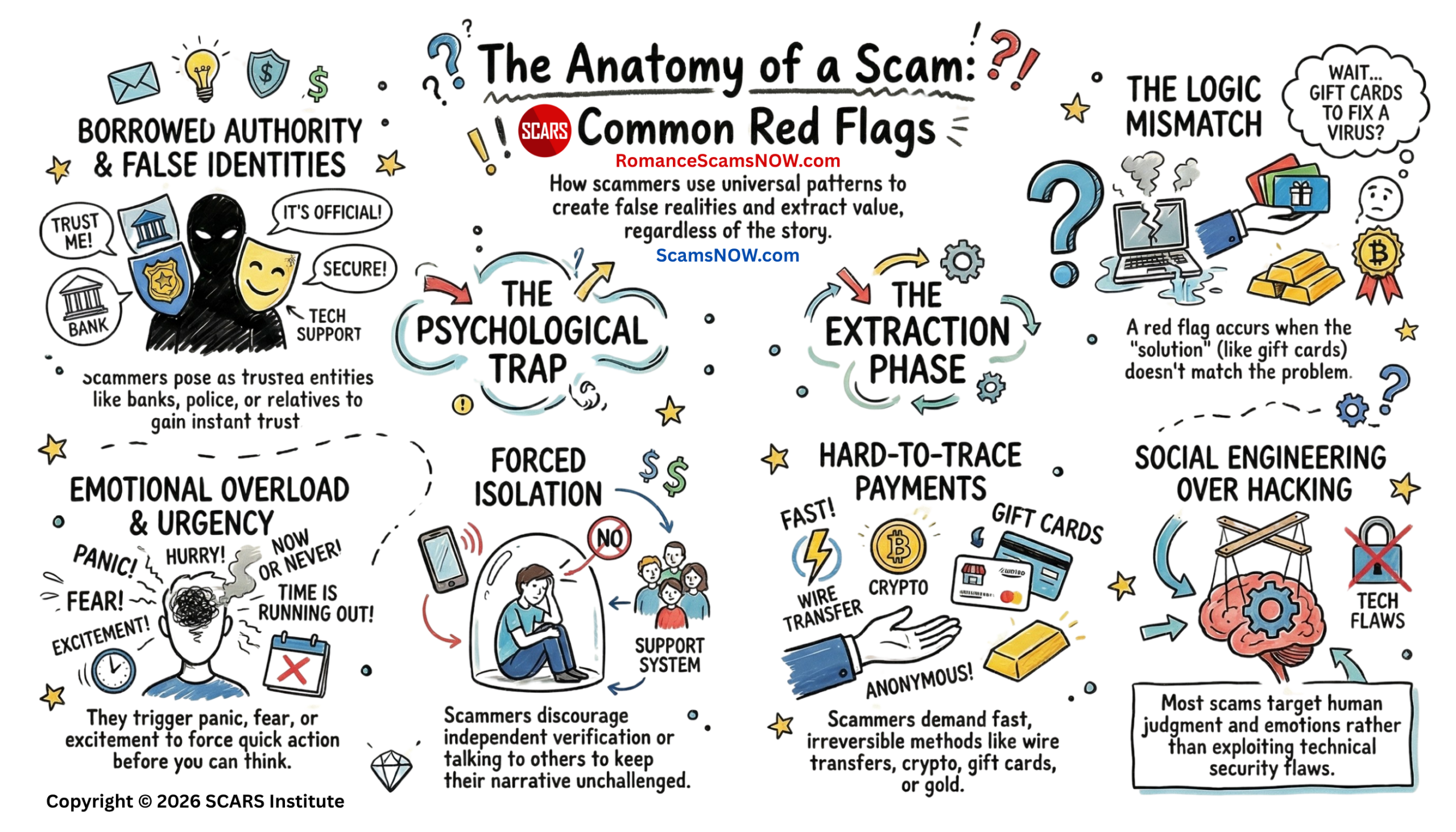
Online and phone scams share a consistent structure built on deception, emotional manipulation, urgency, and control. Scammers present false identities and create believable narratives that introduce problems or opportunities requiring immediate action. Emotional triggers such as fear, hope, or attachment reduce critical thinking, while pressure and secrecy limit verification and outside input. Requests for money, personal information, or access are framed as necessary solutions, often involving fast and irreversible payment methods. Authority, technical language, and familiar branding reinforce credibility, while communication channels enable rapid and widespread contact. Social engineering techniques target human behavior rather than technical systems, and inconsistencies between problems and solutions are masked by urgency and emotional influence. These operations adapt to individual targets but maintain the same underlying goal of controlling perception and behavior long enough to extract value.

15 Things That Nearly Every Online and Phone Scams Have In Common
Things Almost All Online and Phone Scams Seem to Share
Across online scams and phone scams, the details change, but the underlying machinery is remarkably consistent. Whether the approach is a romance scam, bank impersonation, fake tech support, fake delivery alert, crypto fraud, prize scam, or extortion attempt, the same core elements tend to repeat. The FTC, FBI, CISA, and CFPB all describe overlapping warning signs that show up again and again across scam categories.
Here are the 15 things that nearly every online and phone scam has in common:
1. A False Identity
Overview:
Scams almost always begin with deception about who the person is. The scammer may pose as a government agency, bank employee, police officer, relative, employer, tech company, delivery service, romantic interest, or customer support representative. The FTC identifies impersonation as one of the most consistent scam patterns because scammers know trust comes faster when they borrow a real or believable identity.
Detail:
Every online and phone scam begins with deception about identity. The person contacting you is not who they claim to be, and that single fact shapes everything that follows. Scammers may present themselves as bank employees, government officials, law enforcement officers, technical support agents, employers, romantic partners, delivery services, or even trusted companies you recognize. In many cases, they borrow real names, real logos, and real organizational language to strengthen the illusion. Caller ID spoofing, email address mimicry, and cloned social media profiles are common tools used to reinforce that false identity.
This step is not just a surface trick. It is the foundation of psychological compliance. When a message appears to come from a trusted authority or a familiar role, your brain naturally lowers its defenses. You may respond more quickly, question less, and assume legitimacy before verification. This is a normal human response rooted in social conditioning. People are trained to trust institutions, respect authority, and respond to perceived relationships. Scammers exploit that conditioning deliberately.
In many cases, the false identity evolves during the interaction. A scammer may begin as one role and later shift into another if needed. For example, a “bank representative” may escalate to a “fraud investigator” or “law enforcement officer” to increase pressure. In relationship scams, the identity is often built over time, with photos, stories, and emotional engagement used to create a convincing persona.
The key pattern is that identity is always constructed, never authentic. Every scam depends on that initial misrepresentation to gain access to your attention and trust. Without it, the rest of the manipulation would fail almost immediately.
2. An Invented Story that Creates a Problem or Opportunity
Overview:
Every scam needs a narrative. The story may be “your account is compromised,” “you owe money,” “you won a prize,” “your grandson is in trouble,” “your package is delayed,” or “this investment will make you rich.” The story is the delivery system for the fraud. The FTC notes that scammers reuse whatever story gets people to act before they think.
Detail:
Every scam relies on a narrative. The story is what gives the interaction meaning and direction. Without a believable story, there is no reason for you to act. That story may present a problem, such as a compromised account, unpaid taxes, legal trouble, or a family emergency. It may also present an opportunity, such as a prize, investment gain, job offer, or romantic connection. In both cases, the purpose is the same: to create a situation that demands your attention and response.
The structure of these stories is remarkably consistent. They are simple, emotionally engaging, and framed in a way that feels urgent or significant. The details may vary, but the underlying script often includes a trigger event, a consequence, and a proposed solution. For example, “Your account has been hacked” leads to “You may lose your money” followed by “We need you to act now to secure it.” The narrative is designed to move you from awareness to action without pause.
Scammers frequently reuse and adapt these stories. A successful script can be modified for different audiences while keeping the same core structure. A romance scam narrative may involve hardship, travel barriers, or medical emergencies. A business email compromise may involve urgent payments or invoice changes. The surface details change, but the narrative mechanics remain stable.
Importantly, the story is not meant to withstand deep scrutiny. It is meant to be accepted quickly under emotional pressure. Once accepted, even temporarily, it becomes the frame through which all further information is interpreted. That is why the story is introduced early and reinforced throughout the interaction. It anchors the entire scam.
3. An Attempt to Trigger Emotion Before Thought
Overview:
Scammers usually aim for fear, panic, hope, greed, love, pity, shame, or urgency. The FBI specifically warns that scammers often create a false sense of urgency or isolation because strong emotion reduces careful judgment. That emotional jolt is not incidental; it is one of the main tools of control.
Detail:
Emotion is the primary engine of victim compliance in scams. Before logic has time to engage, scammers aim to trigger a strong emotional reaction that shifts your mental state. This may be fear, panic, urgency, excitement, hope, love, sympathy, or even embarrassment. Each emotion serves a different function, but all of them reduce your ability to analyze the situation carefully.
Fear and panic are often used in impersonation scams. You may be told that your account is compromised, that you are under investigation, or that immediate action is required to avoid serious consequences. These emotions narrow your focus and push you toward quick decisions. Hope and excitement are used in prize and investment scams, where the possibility of gain creates a sense of urgency and anticipation. Love and attachment are central in relationship scams, where emotional bonding gradually replaces skepticism. Sympathy is used in hardship stories, where you feel compelled to help.
This emotional activation is not accidental. It directly affects cognitive processing. Under strong emotional arousal, the brain tends to rely on shortcuts rather than careful reasoning. Attention becomes selective, and contradictory information may be ignored or minimized. This makes it easier for the scammer’s narrative to take hold.
Once emotion is engaged, it is continuously reinforced. The scammer may escalate the situation, introduce new emotional triggers, or maintain pressure to keep you in that state. The goal is to prevent a return to calm, reflective thinking, because that is where the scam is most likely to be recognized and stopped.
4. Pressure to Act Quickly
Overview:
Urgency is one of the clearest constants. The victim is told to act now, not later: today, within minutes, before arrest, before account closure, before missing a deal, or before a loved one is harmed. The FTC lists pressure to act immediately as one of the core signs of a scam, and the FBI’s fraud guidance says the same.
Detail:
Urgency is one of the most consistent elements across all scams. You are told that you must act immediately, often within minutes or hours, or you will face negative consequences or miss an important opportunity. This pressure is not simply about speed. It is about limiting your ability to think, verify, and consult others.
When time is compressed, the brain shifts into a more reactive mode. There is less opportunity to cross-check information, question inconsistencies, or seek outside input. This is exactly what the scammer wants. The faster you act, the less likely you are to notice red flags. Urgency also creates a sense of artificial importance, making the situation feel more serious than it actually is.
The language used to create urgency is often direct and repetitive. Phrases like “act now,” “this is your final notice,” “your account will be closed today,” or “you must respond immediately” are common. In some cases, countdowns or deadlines are introduced to intensify the pressure. In relationship scams, urgency may appear as sudden emergencies that require immediate financial help.
Importantly, legitimate organizations rarely require instant action in the way scammers do. Real institutions provide time for verification and decision-making. The insistence on immediate action is a key indicator that the situation is being manipulated.
Urgency works because it bypasses the normal decision-making process. Instead of evaluating options, you are pushed into a single path of action. That path is always designed to benefit the scammer.
5. An Effort to Stop Independent Verification
Overview:
Scammers do not want the target to pause, hang up, call the real institution, log in through the official website, or ask a trusted person. CFPB guidance warns that a major red flag is when a caller discourages verification, support, or counsel from others. In practice, scams survive only as long as reality is kept out of the conversation.
Detail:
Scammers actively work to prevent you from verifying their claims. Verification is one of the most powerful defenses against fraud, so it must be neutralized early. This may involve discouraging you from contacting the real organization, preventing you from hanging up the call, or creating reasons why outside input is unnecessary or dangerous.
You may be told that calling the bank directly will delay the process, that speaking to others will compromise the situation, or that the matter is confidential. In phone scams, the scammer may keep you on the line continuously, guiding you step by step to prevent you from pausing and thinking. In online scams, they may direct you to fake websites or provide alternative contact information that leads back to them.
This isolation from verification is critical. Once you step outside the scammer’s controlled environment, the illusion often collapses quickly. A simple call to the real institution or a conversation with a trusted person can expose inconsistencies and stop the scam.
Scammers may also create false verification mechanisms. They might provide fake badge numbers, case numbers, or links that appear official. These are designed to give you a sense of reassurance without actually allowing independent confirmation.
The goal is to keep you within a closed loop of information controlled by the scammer. As long as that loop remains intact, the narrative can continue unchallenged. Breaking that loop is often the turning point where the scam is recognized.
6. Some Form of Secrecy or Isolation
Overview:
Many scams include “don’t tell anyone,” “stay on the line,” “this is confidential,” or “your family must not know.” The FTC explicitly warns that scammers may insist on secrecy because talking to another person may break the spell. Isolation protects the scammer’s narrative from challenge.
Detail:
Secrecy is a common and powerful tool in scams. You may be instructed not to tell anyone about the interaction, or you may feel that the situation is too sensitive or embarrassing to share. This creates a form of isolation that protects the scam from outside interference.
In some cases, the scammer explicitly demands secrecy. They may say that the matter is confidential, that discussing it could cause problems, or that others would not understand. In other cases, secrecy is implied through the nature of the situation. For example, a threat of legal trouble or a promise of a large reward may lead you to keep the interaction private.
Isolation has a strong psychological effect. When you are not discussing the situation with others, you are more likely to rely on the information provided by the scammer. There is no external perspective to challenge the narrative or point out inconsistencies. This makes it easier for the scam to continue.
In relationship scams, isolation can develop gradually. The scammer may encourage emotional dependence and reduce your connection to others. Over time, the scammer becomes the primary source of information and support, making it harder to question their intentions.
Secrecy also reduces the likelihood of early intervention. Friends, family, or colleagues who might recognize the signs of a scam are kept out of the situation. By the time the scam is revealed, significant harm may already have occurred.
7. A Request for Money, Information, Access, or All Three
Overview:
The end goal is always extraction. Sometimes it is direct theft of money. Sometimes it is personal information, bank details, Social Security numbers, passwords, account verification codes, or remote access to a phone or computer. Even when the scam looks social or romantic at first, the operation usually moves toward money, usable identity data, or account access.
Detail:
At its core, every scam is about extraction. The scammer’s goal is to obtain something of value from you. This may be direct financial payment, personal information, account credentials, or access to your devices and systems. Sometimes it involves all of these elements in combination.
The request may be presented in different ways depending on the type of scam. In some cases, it is direct, such as a demand for payment to resolve an issue or secure a benefit. In other cases, it is gradual, with small requests building over time. In relationship scams, financial requests may begin as minor assistance and escalate into larger transfers.
Information requests are equally important. Personal data, verification codes, passwords, and account details can be used to access financial accounts or commit identity fraud. In some scams, gaining access to your computer or phone allows the scammer to control your accounts directly.
The request is often framed as necessary or helpful. You may be told that providing information will protect your account, that sending money will resolve a problem, or that granting access will fix a technical issue. These explanations are designed to make the request seem reasonable and justified.
Regardless of the form it takes, the request is always aligned with the scammer’s objective. It is the point where the manipulation translates into tangible gain.
8. A Payment Method that is Fast, Hard to Reverse, or Hard to Trace
Overview:
Scammers strongly prefer payment methods that reduce the victim’s chance of recovery. The CFPB and FTC repeatedly warn about wire transfers, money transfers, P2P apps, gift cards, cryptocurrency, cash, and even gold handed to couriers. Those methods are attractive to scammers because they are quick and often difficult to claw back.
Detail:
Scammers prefer payment methods that minimize the chances of recovery. These methods are typically fast, irreversible, and difficult to trace. Common examples include wire transfers, money transfer services, gift cards, cryptocurrency, and peer-to-peer payment apps.
The choice of payment method is not random. It is carefully selected to reduce risk for the scammer. Once the payment is made, it is often moved quickly through multiple accounts or converted into other forms, making it difficult to track or recover.
Gift cards are a common example. They are widely available, easy to purchase, and can be converted into usable funds quickly. Cryptocurrency offers a similar advantage, with transactions that can be difficult to reverse and trace. Wire transfers and money transfers provide speed and global reach.
Scammers often provide detailed instructions on how to make the payment. They may guide you step by step, sometimes staying on the phone while you complete the transaction. This ensures that the process is completed without interruption.
Legitimate organizations rarely require these types of payments, especially in urgent or unusual situations. The insistence on a specific, non-reversible payment method is a strong indicator of a scam.
9. A Claim of Authority, Legitimacy, or Technical Expertise
Overview:
Even when the scammer is pretending to be helpful, the message usually carries borrowed authority. They may use a government seal, caller-ID spoofing, employee ID numbers, official-sounding language, fake invoices, or technical jargon. The goal is to make the target defer rather than question. FTC guidance on imposters highlights fake caller ID, official-looking documents, and the names of real agencies or employees as common tactics.
Detail:
Authority plays a central role in many scams. By presenting themselves as figures of authority or expertise, scammers increase their credibility and reduce resistance. This may involve claiming to be from a government agency, financial institution, law enforcement, or a well-known company.
The appearance of authority is reinforced through language, tone, and presentation. Scammers may use formal language, technical terms, and structured communication to create a sense of professionalism. They may provide identification numbers, case references, or official-sounding titles.
Visual elements are also used to support this claim. Emails may include logos, signatures, and formatting that mimic real organizations. Websites may be designed to look legitimate, with familiar branding and layout. Caller ID spoofing can make phone calls appear to come from trusted sources.
Authority influences behavior. People are more likely to comply with requests from perceived authority figures, especially in situations that involve risk or uncertainty. This is a well-documented psychological effect that scammers exploit.
The claim of expertise is often used in technical support scams. The scammer presents themselves as someone who understands the problem and can provide a solution. This creates a dependency on their guidance, making it easier to direct your actions.
10. A Communication Channel Chosen for Reach and Speed
Overview:
Online and phone scams depend on channels that let scammers contact many people cheaply and quickly: phone calls, texts, email, social media, messaging apps, dating platforms, pop-ups, and fake websites. CISA and the FTC describe phishing and social engineering as scalable forms of deception because one criminal can cast a wide net and adapt scripts instantly.
Detail:
Scams rely on communication channels that allow scammers to reach large numbers of people quickly and at low cost. These channels include phone calls, text messages, email, social media, messaging apps, and online platforms. The choice of channel is strategic and often based on the target audience.
Phone calls provide direct interaction and immediate engagement. Text messages offer speed and simplicity, often used for short, urgent messages. Email allows for detailed communication and the inclusion of links and attachments. Social media and messaging apps enable scammers to build relationships and maintain ongoing contact.
These channels also allow for automation and scaling. A single scammer can send thousands of messages or make numerous calls in a short period. This increases the chances of finding individuals who will respond.
The channel also influences the style of the scam. For example, phishing emails often include links to fake websites, while phone scams rely on real-time interaction and pressure. Social media scams may involve longer-term engagement and relationship building.
The common factor is that the channel is chosen to maximize efficiency and effectiveness. It allows the scammer to initiate contact, deliver the narrative, and guide the interaction toward the desired outcome.
11. Social Engineering Rather than Pure Technical Skill
Even when technology is involved, most scams rely more on manipulating human judgment than on sophisticated hacking. CISA defines phishing and related attacks as deceptive attempts to get people to share information or take unsafe actions. In other words, the human mind is usually the primary target, and the device is only the route in.
Detail:
Most scams rely more on psychological manipulation than on advanced technical methods. This approach, known as social engineering, focuses on influencing human behavior rather than exploiting technical vulnerabilities.
Social engineering involves understanding how people think, feel, and respond to different situations. Scammers use this knowledge to craft messages and interactions that guide you toward specific actions. This may involve building trust, creating urgency, or exploiting emotions.
While technology is often involved, it is usually a tool rather than the primary mechanism. For example, a phishing email may use a fake website, but the success of the scam depends on convincing you to click the link and enter your information.
This approach is effective because it targets the human element, which is often more flexible and less predictable than technical systems. It also allows scammers to adapt quickly to different situations and targets.
Understanding that scams are primarily psychological can help in recognizing and resisting them. It shifts the focus from technical details to the underlying patterns of manipulation.
12. A Mismatch Between the Claimed Problem and the Demanded Solution
Overview:
This is one of the most reliable common denominators. If the claimed issue is account fraud, the “solution” should be contacting the real bank through official channels, not buying gift cards or moving savings to a stranger. If the claimed caller is the FTC, the agency will not ask for money to “protect” it. FTC warnings repeatedly emphasize that legitimate institutions do not solve problems the way scammers say they do.
Detail:
One of the most reliable indicators of a scam is a mismatch between the problem presented and the solution offered. The scenario may seem plausible at first, but the required action does not align with how legitimate processes work.
For example, if a bank account is compromised, the appropriate response would involve contacting the bank through official channels and following established procedures. A request to transfer money to a “safe account” or purchase gift cards does not align with legitimate banking practices.
This mismatch often becomes clearer upon closer examination. The solution may involve unusual steps, unfamiliar processes, or actions that feel inconsistent with the situation. However, under pressure and emotional influence, these inconsistencies may be overlooked.
Scammers rely on this gap between perception and reality. They present a believable problem and then guide you toward an illogical solution. The effectiveness of this approach depends on maintaining the emotional and cognitive conditions that prevent critical evaluation.
Recognizing this mismatch can be a powerful tool in identifying scams. It encourages a pause and a reassessment of whether the requested action makes sense in the context of the problem.
13. A Push to Override Normal Skepticism
Overview:
Scammers try to get the target to suspend the ordinary rules they would apply in any other setting. They want the victim to ignore inconsistencies, excuse odd payment demands, overlook strange grammar, accept spoofed numbers, or trust a stranger’s explanation more than their own instincts. CISA’s phishing guidance specifically points to suspicious sender addresses, generic greetings, odd links, and other small irregularities that people are pressured to overlook.
Detail:
Scammers actively work to reduce your natural skepticism. This involves encouraging you to ignore doubts, overlook inconsistencies, and accept information without verification. The goal is to create a state where questioning feels unnecessary or even inappropriate.
This may be achieved through reassurance, repetition, and the presentation of seemingly credible details. The scammer may address potential concerns preemptively, providing explanations that make the situation appear legitimate. They may also use social proof, suggesting that others have already complied or benefited.
Pressure and urgency also play a role in overriding skepticism. When you feel that immediate action is required, there is less opportunity to question the situation. Emotional engagement further reduces critical thinking, making it easier to accept the narrative.
In some cases, skepticism is reframed as a problem. You may be told that hesitation could cause harm, delay resolution, or result in missed opportunities. This shifts the focus from questioning to compliance.
Maintaining skepticism requires conscious effort, especially under pressure. Recognizing attempts to override it can help restore a more balanced and critical perspective.
14. Adaptability to the Victim
Overview:
Scams are highly flexible. The same underlying playbook can be adjusted to a young job seeker, an older adult, a business employee, a recent scam victim, a lonely person, or someone frightened about fraud on an account. The FBI and CFPB both describe recurring tactics that show up across very different fraud categories because scammers tailor the surface details to the target while keeping the same psychological structure.
Detail:
Scams are highly adaptable. While the core structure remains consistent, the details are tailored to the individual target. This customization increases the likelihood of success by aligning the scam with the target’s interests, concerns, and circumstances.
Scammers may gather information from public sources, social media, or previous interactions to personalize their approach. They may adjust their language, tone, and narrative to match the target’s profile. For example, a job seeker may receive a fake employment offer, while a business employee may receive a request related to invoices or payments.
This adaptability extends to the progression of the scam. The scammer may change tactics based on your responses, introducing new elements or adjusting the story as needed. This flexibility allows the scam to continue even when initial approaches are challenged.
The ability to adapt is a key strength of scams. It allows them to remain effective across different contexts and populations. It also makes them harder to detect, as they do not follow a single fixed pattern.
Understanding this adaptability can help in recognizing that even personalized interactions may still follow the same underlying structure as other scams.
15. A Final Goal of Control
Overview:
At bottom, every scam is an attempt to control a person’s attention, emotions, decisions, and behavior long enough to extract value. Money is the usual prize, but the real engine is coercive control over perception and action: keeping the victim engaged, compliant, and cut off from correction. That is why urgency, secrecy, impersonation, false authority, and irreversible payment methods recur so consistently across both online and phone scams. This is an inference drawn from the repeated warning patterns described by the FTC, FBI, CISA, and CFPB.
Detail:
At the deepest level, every scam is about control. The scammer seeks to influence your attention, emotions, and actions in a way that leads to a specific outcome. This control is maintained throughout the interaction, from the initial contact to the final extraction.
Control is established through a combination of the elements described above. False identity creates trust. The story provides context. Emotion and urgency drive action. Isolation prevents interference. Authority reinforces compliance. Each element contributes to maintaining influence over your decisions.
This control is often temporary but highly effective. It does not require long-term dominance, only enough influence to achieve the scammer’s objective. Once that objective is met, the control is no longer needed.
Recognizing the role of control shifts the perspective from individual tactics to the overall structure of the scam. It highlights the importance of maintaining autonomy, seeking verification, and resisting pressure.
Ultimately, scams succeed not because of a single tactic, but because of a coordinated effort to shape perception and behavior. Understanding this can provide a stronger foundation for prevention and response.
Review
The simplest way to summarize all 15 is this: every scam tries to create a false reality, rush you inside it, block outside reality checks, and get something valuable from you before the illusion breaks. That pattern holds whether the contact comes by phone, text, email, social media, dating app, or fake website.
Conclusion
When these patterns are viewed together, a clear structure emerges that explains why scams are so effective across different formats and audiences. Each element reinforces the others. A false identity lowers initial resistance. A compelling story provides context. Emotional activation reduces careful thinking. Urgency accelerates decisions. Isolation prevents correction. The requested action then converts that influence into real-world loss. None of these elements operates alone. They function as an integrated system designed to guide behavior step by step until compliance is achieved.
This structure also explains why intelligent, careful people can still be deceived. The process is not based on a lack of knowledge. It is based on temporary shifts in attention, emotion, and decision-making. Under pressure, the brain prioritizes immediate response over careful evaluation. When verification is blocked and outside input is removed, the false narrative can feel real enough to act upon.
Understanding these shared elements changes how scams are recognized. Instead of focusing on the surface details, such as the specific story or method, attention can shift to the underlying pattern. When urgency appears with secrecy, when authority is combined with unusual payment demands, or when emotion overrides logic, the structure becomes visible.
This awareness does not eliminate risk, but it creates a pause. That pause allows for verification, outside perspective, and restoration of control. In that moment, the scam begins to lose its power.

Glossary
- Account Compromise Narrative — This term refers to a structured storyline used to convince a victim that a financial or personal account has been breached or is at risk. The narrative is designed to create fear and urgency, which may override careful thinking and encourage immediate action. The scammer presents a solution that appears protective but actually redirects control away from legitimate institutions. Recognizing this pattern may help a victim pause and verify the situation through official channels.
- Authority Claim — This term describes the presentation of power, status, or expertise to influence a victim’s behavior. Scammers often claim to represent government agencies, financial institutions, or technical services to create automatic trust. This perceived authority may reduce skepticism and increase the likelihood of compliance without verification. Awareness of this tactic may help a victim question the legitimacy of the source before acting.
- Behavioral Control — This term refers to the structured process of directing a victim’s actions step by step throughout a scam interaction. The scammer uses emotional pressure, urgency, and limited information to guide decisions in a predictable sequence. Each instruction builds on the previous one, reducing independent thinking and increasing compliance. Understanding this process may help a victim recognize when their behavior is being influenced rather than freely chosen.
- Caller ID Spoofing — This term refers to the manipulation of phone display information to make a call appear as if it originates from a trusted source. Scammers use this technique to imitate banks, government agencies, or known contacts. The familiar number may create a false sense of legitimacy and reduce suspicion. Recognizing that caller ID can be falsified may help a victim rely on independent verification instead of displayed information.
- Cognitive Shortcuts — This term describes mental processes that allow individuals to make quick decisions without full analysis. Scammers exploit these shortcuts by creating urgency and emotional intensity, which reduces careful evaluation. When cognitive shortcuts are activated, individuals may rely on assumptions rather than evidence. Awareness of this tendency may help a victim slow down and reassess the situation.
- Communication Channel Selection — This term refers to the deliberate choice of platforms such as phone, email, text, or social media to deliver scam messages. Scammers select channels that allow rapid contact and broad reach with minimal effort. Each channel supports different forms of interaction, from immediate pressure to long-term engagement. Understanding this selection may help a victim recognize that the medium itself can be part of the manipulation.
- Compliance Conditioning — This term describes the gradual shaping of a victim’s willingness to follow instructions over time. Scammers often begin with small, low-risk requests that appear harmless or reasonable. As trust develops, the requests become more significant and demanding. Recognizing this progression may help a victim identify when cooperation is being deliberately increased.
- Constructed Identity — This term refers to the creation of a detailed false persona used to gain trust and credibility. The identity may include names, roles, images, and personal stories that appear consistent and believable. This constructed persona is maintained throughout the interaction to reinforce legitimacy. Awareness of this tactic may help a victim question whether the identity can be independently verified.
- Control Loop — This term describes a closed system in which the scammer provides all information, instructions, and explanations. The victim is encouraged to rely solely on this source and avoid outside input. This loop prevents contradictory information from being introduced and reinforces the scam narrative. Recognizing this pattern may help a victim seek external verification and break the cycle.
- Credibility Signals — This term refers to visual and verbal cues that create an impression of legitimacy during a scam. These signals may include official logos, formal language, structured communication, and technical terminology. Such elements are designed to reduce skepticism and increase trust. Awareness of these signals may help a victim distinguish between appearance and actual authenticity.
- Decision Compression — This term describes the reduction of time available for thoughtful decision-making during a scam. Scammers create artificial deadlines or urgent situations to force rapid responses. This limits the ability to verify information or consider alternatives. Recognizing this pressure may help a victim slow down and regain control over the decision process.
- Emotional Activation — This term refers to the deliberate triggering of strong feelings to influence a victim’s behavior. Scammers may use fear, hope, love, or urgency to shift attention away from logical analysis. These emotional states can reduce critical thinking and increase impulsive action. Understanding this effect may help a victim pause and evaluate the situation more carefully.
- Emotional Reinforcement — This term describes the ongoing use of emotional triggers to maintain a specific mental state during a scam. The scammer may introduce new details or escalate the situation to sustain emotional intensity. This prevents a return to calm, reflective thinking. Awareness of this pattern may help a victim recognize when emotions are being manipulated.
- Escalation Strategy — This term refers to the gradual increase in demands or pressure as a scam progresses. Initial requests may appear minor or reasonable, which helps build trust and compliance. Over time, the requests become larger, more urgent, or more risky. Recognizing this escalation may help a victim identify when the situation is moving beyond normal boundaries.
- Extraction Objective — This term describes the ultimate goal of obtaining something of value from the victim. This may include money, personal information, account credentials, or device access. All elements of the scam are directed toward achieving this outcome. Understanding this objective may help a victim recognize that the interaction is designed for exploitation.
- False Authority Presentation — This term refers to the use of titles, roles, or affiliations to appear credible and trustworthy. Scammers may claim to represent institutions that people are conditioned to trust. This presentation encourages compliance and reduces questioning. Awareness of this tactic may help a victim verify authority before responding.
- False Narrative Framework — This term describes the structured story that guides a scam interaction. The framework typically includes a problem, a consequence, and a proposed solution. This structure provides context and direction, making the situation appear logical and urgent. Recognizing this framework may help a victim question whether the narrative aligns with reality.
- Financial Redirection — This term refers to the movement of funds away from legitimate accounts under the pretense of protection or necessity. Victims may be instructed to transfer money to a different account or method. In reality, this action places control in the hands of the scammer. Understanding this tactic may help a victim avoid transferring funds without verification.
- Identity Evolution — This term describes the change or adaptation of a scammer’s persona during an interaction. The scammer may shift roles to increase credibility or apply additional pressure. This flexibility helps maintain control and address doubts. Recognizing this behavior may help a victim question inconsistencies in identity.
- Information Isolation — This term refers to limiting access to external perspectives or sources of verification. Victims may be encouraged to rely only on the scammer’s instructions and avoid discussing the situation with others. This isolation prevents contradictory information from being introduced. Awareness of this tactic may help a victim seek outside input.
- Instruction Sequencing — This term describes the step-by-step guidance provided to lead a victim through a scam. Each instruction builds on the previous one, creating a clear path of action. This sequencing reduces uncertainty and increases compliance. Recognizing this pattern may help a victim pause and reassess the overall situation.
- Legitimacy Illusion — This term refers to the overall impression that a scam interaction is genuine and trustworthy. It is created through consistent messaging, credible details, and professional presentation. This illusion reduces suspicion and encourages engagement. Awareness of this effect may help a victim look beyond appearances.
- Manipulation Pattern — This term describes the recurring structure found across many scams. It includes identity deception, emotional triggers, urgency, and extraction. Recognizing this pattern may help identify scams even when details differ. This understanding provides a broader perspective on how scams operate.
- Narrative Anchoring — This term refers to the establishment of a central story that shapes how all information is interpreted. Once accepted, the narrative influences perception and decision-making. This makes it more difficult to question or challenge the situation. Awareness of this effect may help a victim reconsider the initial premise.
- Payment Irreversibility — This term describes the use of payment methods that are difficult or impossible to recover once completed. Scammers prefer options that cannot be easily traced or reversed. This ensures that the loss remains final. Recognizing this characteristic may help a victim question unusual payment requests.
- Payment Method Manipulation — This term refers to directing a victim toward specific payment options chosen by the scammer. These methods are selected for speed, anonymity, and lack of recovery options. The scammer often provides detailed instructions to ensure compliance. Awareness of this tactic may help a victim resist unfamiliar payment demands.
- Perceived Urgency — This term describes the feeling that immediate action is required to avoid negative consequences. Scammers create this perception through language and situational framing. This urgency reduces the likelihood of careful evaluation. Recognizing this feeling may help a victim slow down and verify information.
- Persona Development — This term refers to the detailed creation of a believable character used in a scam. The persona may include personal stories, images, and consistent communication patterns. This development builds trust over time, especially in long-term scams. Awareness of this process may help a victim question the authenticity of the relationship.
- Pressure Language — This term describes specific wording used to create urgency and compel action. Phrases emphasize immediacy, consequences, or limited time. This language influences perception and behavior. Recognizing these phrases may help a victim identify manipulation.
- Psychological Compliance — This term refers to the tendency to follow instructions under certain conditions. Factors such as authority, urgency, and emotional influence increase compliance. Scammers create environments that encourage this response. Awareness of this tendency may help a victim maintain independent judgment.
- Reality Distortion — This term describes the temporary alteration of perception during a scam interaction. The false narrative may feel real and convincing under pressure. This distortion affects decision-making and judgment. Recognizing this effect may help a victim pause and reassess.
- Remote Access Request — This term refers to asking for control over a device or system under the pretense of assistance. Scammers may claim this is necessary to fix a problem or provide support. Granting access allows direct manipulation of accounts or data. Awareness of this risk may help a victim refuse such requests.
- Response Acceleration — This term describes the increase in speed of reactions due to pressure or urgency. Victims may act quickly without full consideration. This reduces opportunities for verification. Recognizing this pattern may help a victim slow down and regain control.
- Risk Minimization Framing — This term refers to presenting harmful actions as protective or beneficial. Scammers may claim that compliance will reduce risk or prevent loss. This framing makes dangerous actions appear reasonable. Awareness of this tactic may help a victim question the proposed solution.
- Script Reuse — This term describes the repeated use of successful scam narratives across different targets. Scammers adapt proven scripts to fit various situations. This consistency reflects the effectiveness of certain approaches. Recognizing familiar patterns may help identify scams more quickly.
- Secrecy Enforcement — This term refers to actively discouraging a victim from sharing information about the interaction. Scammers may claim confidentiality or create fear of consequences. This prevents outside intervention and verification. Awareness of this tactic may help a victim seek trusted advice.
- Social Conditioning Exploitation — This term describes the use of learned social behaviors to influence actions. People are conditioned to trust authority and respond to requests for help. Scammers exploit these tendencies to gain compliance. Recognizing this influence may help a victim question automatic responses.
- Social Engineering — This term refers to the manipulation of human behavior to achieve a specific goal. It relies on psychological techniques rather than technical methods. Scammers use social engineering to guide decisions and actions. Understanding this concept may help a victim recognize manipulation.
- Story Consistency Maintenance — This term describes keeping the scam narrative coherent throughout the interaction. Consistency reinforces believability and reduces suspicion. The scammer adjusts details to maintain alignment with the story. Awareness of this tactic may help a victim identify inconsistencies.
- Suspicion Suppression — This term refers to reducing doubts and concerns during a scam. Scammers address potential questions before they arise. This prevents critical evaluation and maintains trust. Recognizing this behavior may help a victim question reassurance.
- Target Adaptation — This term describes tailoring the scam to fit the individual victim. Scammers adjust language, tone, and content based on available information. This increases relevance and effectiveness. Awareness of this tactic may help a victim recognize personalization as manipulation.
- Technical Legitimacy Signals — This term refers to the use of technical details to appear credible. These may include system messages, error reports, or diagnostic language. Such signals create an impression of expertise and authenticity. Recognizing these cues may help a victim question their validity.
- Time Pressure Framing — This term describes presenting a situation as limited in time to force quick action. The framing emphasizes urgency and consequences. This reduces the likelihood of delay or verification. Awareness of this tactic may help a victim slow down.
- Trust Leveraging — This term refers to using existing trust relationships or recognizable symbols to gain credibility. Scammers mimic institutions or individuals that are already trusted. This reduces skepticism and encourages engagement. Recognizing this tactic may help a victim verify independently.
- Verification Blocking — This term describes preventing independent confirmation of claims. Scammers discourage or redirect attempts to verify information. This maintains control over the narrative. Awareness of this tactic may help a victim insist on verification.
- Victim Targeting — This term refers to selecting individuals based on characteristics that increase susceptibility. Scammers identify vulnerabilities such as emotional state or situational context. This targeting improves the likelihood of success. Recognizing this approach may help a victim understand that selection is strategic, not personal.
Author Biographies
-/ 30 /-
What do you think about this?
Please share your thoughts in a comment below!
LEAVE A COMMENT?
Recent Comments
On Other Articles
- Debby Montgomery Johnson on The Danger of Using AI in Law Enforcement – The Grandmother Wrongly Arrested as a Fraudster – 2026: “Excellent article – I can’t imagine the terror Angela most certainly experienced. Compound this with the lack of accountability by…” Mar 24, 09:20
- on The Crazy Gregor MacGregor and the Country of Poyais Scam – History of Scams – 2026: “interesting” Mar 23, 19:24
- on BEC Fraud Reaches $43 Billion Per Year: “oh my gosh so much of an increase in the fraud I pray the officials can continue tracking and make…” Mar 23, 15:09
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Make Online Safe Again!” Mar 17, 19:11
- on Establishing The United States Task Force To Eliminate Fraud – 2026: “Finally an administration takes the initiative to help solve the gigantic situation. Make America Safe Again, thank you!” Mar 17, 15:41
- on What Is The Difference Between A Scam Victim And A Scam Survivor? [Updated]: “Due to my scams I don’t fully trust anyone online and I shouldn’t even those people I knew in high…” Mar 7, 12:46
- on SCARS 3 Steps For New Scam Victims 2024: “I was very fearful “he” would come to my home because I was knew my address, I spoke to someone…” Mar 7, 09:50
- on Sadness & Scam Recovery: “Before my scam, my mom passed away and I got a divorce, so I was dealing with the loss of…” Mar 7, 09:37
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is NO evidence and she is not, she is a victim too. Sebastian, stop letting your anger think for…” Mar 6, 23:18
- on The Story Of Kira Lee Orsag (aka Dani Daniels) [Updated]: “There is real evidence that behind these two people there is something that not many people know. This woman is…” Mar 4, 03:58
ARTICLE META
Important Information for New Scam Victims
- Please visit www.ScamVictimsSupport.org – a SCARS Website for New Scam Victims & Sextortion Victims
- Enroll in FREE SCARS Scam Survivor’s School now at www.SCARSeducation.org
- Please visit www.ScamPsychology.org – to more fully understand the psychological concepts involved in scams and scam victim recovery
If you are looking for local trauma counselors please visit counseling.AgainstScams.org or join SCARS for our counseling/therapy benefit: membership.AgainstScams.org
If you need to speak with someone now, you can dial 988 or find phone numbers for crisis hotlines all around the world here: www.opencounseling.com/suicide-hotlines
A Note About Labeling!
We often use the term ‘scam victim’ in our articles, but this is a convenience to help those searching for information in search engines like Google. It is just a convenience and has no deeper meaning. If you have come through such an experience, YOU are a Survivor! It was not your fault. You are not alone! Axios!
A Question of Trust
At the SCARS Institute, we invite you to do your own research on the topics we speak about and publish, Our team investigates the subject being discussed, especially when it comes to understanding the scam victims-survivors experience. You can do Google searches but in many cases, you will have to wade through scientific papers and studies. However, remember that biases and perspectives matter and influence the outcome. Regardless, we encourage you to explore these topics as thoroughly as you can for your own awareness.
Statement About Victim Blaming
SCARS Institute articles examine different aspects of the scam victim experience, as well as those who may have been secondary victims. This work focuses on understanding victimization through the science of victimology, including common psychological and behavioral responses. The purpose is to help victims and survivors understand why these crimes occurred, reduce shame and self-blame, strengthen recovery programs and victim opportunities, and lower the risk of future victimization.
At times, these discussions may sound uncomfortable, overwhelming, or may be mistaken for blame. They are not. Scam victims are never blamed. Our goal is to explain the mechanisms of deception and the human responses that scammers exploit, and the processes that occur after the scam ends, so victims can better understand what happened to them and why it felt convincing at the time, and what the path looks like going forward.
Articles that address the psychology, neurology, physiology, and other characteristics of scams and the victim experience recognize that all people share cognitive and emotional traits that can be manipulated under the right conditions. These characteristics are not flaws. They are normal human functions that criminals deliberately exploit. Victims typically have little awareness of these mechanisms while a scam is unfolding and a very limited ability to control them. Awareness often comes only after the harm has occurred.
By explaining these processes, these articles help victims make sense of their experiences, understand common post-scam reactions, and identify ways to protect themselves moving forward. This knowledge supports recovery by replacing confusion and self-blame with clarity, context, and self-compassion.
Additional educational material on these topics is available at ScamPsychology.org – ScamsNOW.com and other SCARS Institute websites.
Psychology Disclaimer:
All articles about psychology and the human brain on this website are for information & education only
The information provided in this article is intended for educational and self-help purposes only and should not be construed as a substitute for professional therapy or counseling.
While any self-help techniques outlined herein may be beneficial for scam victims seeking to recover from their experience and move towards recovery, it is important to consult with a qualified mental health professional before initiating any course of action. Each individual’s experience and needs are unique, and what works for one person may not be suitable for another.
Additionally, any approach may not be appropriate for individuals with certain pre-existing mental health conditions or trauma histories. It is advisable to seek guidance from a licensed therapist or counselor who can provide personalized support, guidance, and treatment tailored to your specific needs.
If you are experiencing significant distress or emotional difficulties related to a scam or other traumatic event, please consult your doctor or mental health provider for appropriate care and support.
Also read our SCARS Institute Statement about Professional Care for Scam Victims – click here to go to our ScamsNOW.com website.













Thank you for your comment. You may receive an email to follow up. We never share your data with marketers.