SCARS FAQs – Frequently Asked Questions About Scams & Scammers
Select FAQs By Category
It shows the first 25 FAQs. Use the filters to see more!
- All
- About SCARS
- About Technology
- Basics
- Cybersecurity/Cybercrime Related
- Intro
- Law Enforcement Regulation & Governance
- Money Mules
- Money Recovery
- Online Safety
- Other Participants
- Psychology of Scams
- Reporting Scams & Enforcement
- Romance Scams Related
- Scam Types
- Scammers/Fraudsters
- Spotting & Avoiding Scams
- Victim-Survivor Questions
- Victims' Issues
- Victims' Support & Recovery
SCARS™ Anti-Scam FAQ: “Can You Hear Me?” and “Yes” Calls
This scam happens when you answer the phone, and the person on the other line asks: “Can you hear me?” and you respond, “Yes.” Your voice is being recorded to obtain a voice signature for scammers authorize fraudulent charges over the phone. You can visit the FCC website to block any unwanted calls. The BBB Scam Tracker received more than 10,000 reports on the “Can you hear me?” scam, but none of the reports resulted in an actual loss of money.
Anti-Scam FAQ: What Is “Your Order Has Arrived”/Shipping Status Scam
Answer:
You may have received an email that says your “order” from Amazon or other ecommerce retailer has arrived or has been shipped. It likely asks you to click on a link.
SCARS™ Anti-Scam FAQ: Airbnb Scam
This scam takes advantage of travelers renting an apartment or house through Airbnb by featuring fake homes on the site and directing the renter to a fraudulent or “spoof” website to finalize payment. Scammers will often even trick real owners, who don’t know their property is being spoofed. Potential travelers end up paying money for a rental property that either doesn’t exist or isn’t available.
SCARS™ Anti-Scam FAQ: Amazon Fake Order Cancellation Emails
If you get an email about an order cancellation from Amazon.com, there’s a good chance it’s a scam. Click on links in the email and you could unintentionally download malware onto your device. Or you might be sent to a site that aims to collect your Amazon account information, like your username and password. If you receive such an email and recently placed an order, go to Amazon.com to check your order status.
Anti-Scam FAQ: What Is An Antivirus Scam?
Answer:
People are cold called and told they have a problem with their computer which, for a fee, can be fixed. Alternatively, the victim might initiate the contact in response to an online advert or prompt claiming that their device has been infected with a virus. Other computer scam methods involve offering bogus virus protection or warranties
SCARS™ Anti-Scam FAQ: Apple Care Scam
This new smartphone scam uses phishing emails to send Apple users to a fake Apple website. iPhone users receive a pop-up image of a system dialog box that tells users their phone has been “locked for illegal activity.” When users click on the link, scammers enroll them into a fraudulent “mobile device management service” that allows scammers to send malware apps to iPhones. Read more here about phishing scams and how to spot them.
Application Fraud (New Account Fraud)
Application fraud is the unauthorized opening of a new account leveraging compromised identity information. This can be for a variety of accounts, including credit cards, retail bank accounts, consumer lending and much more.
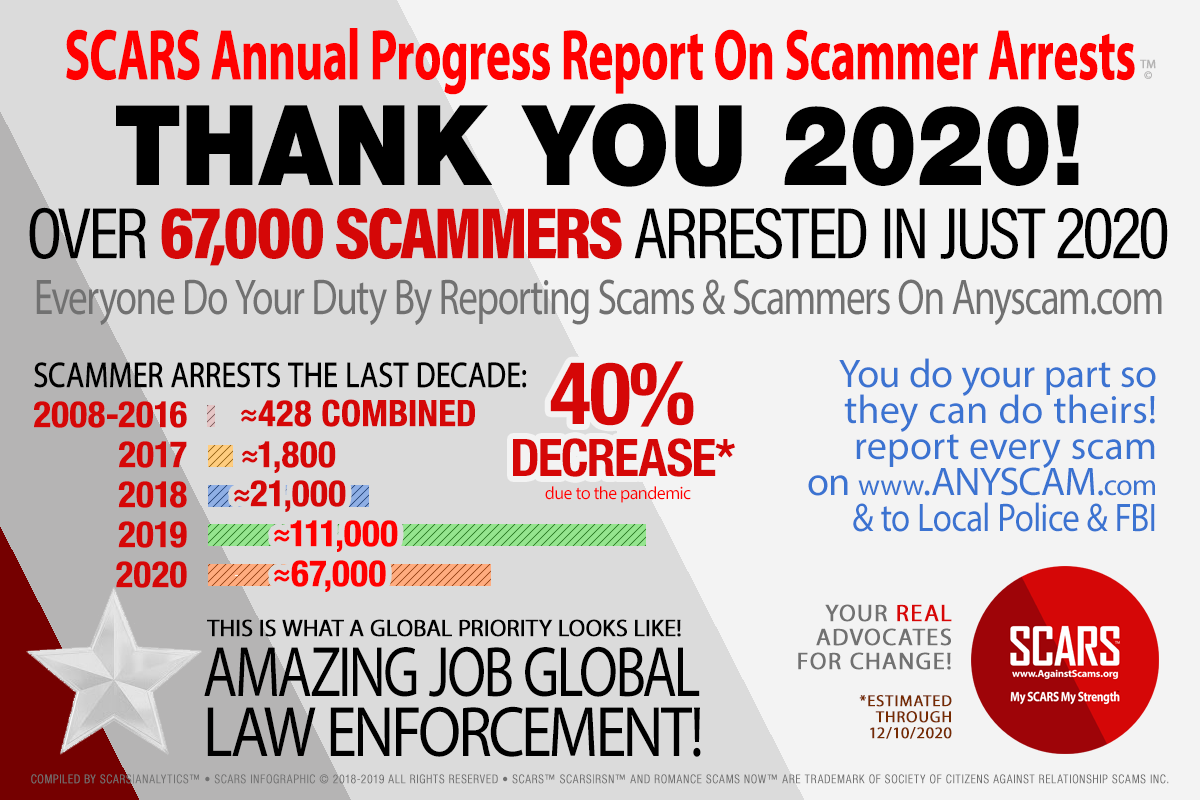
Anti-Scam FAQ: How Are Most Scammers Arrested
Answer:
Scammers are typically arrested in one of five ways:
- Victim Reporting
The reports that victims make through the various agencies (local police, national police, Anyscam.com) all accumulates – it may not result in immediate action but over time it identifies individual scammers or organizations. Once the law enforcement agency has enough to identify someone they can begin an investigation that can lead to arrests. This is why victim reporting is so important. Right now, only about 3% of victims report these crimes. - Connection to Other Scammers
When one scammer is arrested all of their connections are looked at carefully. If the scammer had connections that also involved suspected crimes it allows law enforcement to roll up whole organizations in this way. One identification can lead to hundreds, including their leadership. - Obvious Lifestyle
Most scammers are business people and understand the need to stay below the radar, but there is always one in every group that wants to live large. They show off their new money with cars, jewelry, friends, entertainment, houses, and more. In other words, they make it obvious that they are spending more money than they earn – this allows law enforcement to investigate them for tax evasion, and if they confirm they spend more than they have income for they can be arrested for that. - Tips & Partnerships
Law enforcement agencies have relationships (usually confidential) with other organizations, NGOs, or entities) that regularly feed them with information. Or they receive tips from the public about individual scammers or groups. All of these allow law enforcement agencies to begin investigations that can lead to arrests. - Scammers Turn On Each Other
The over-riding motivation with fraudsters is greed – if they feel that they have not been fairly treated they can and do report each other to law enforcement. There is no honor among thieves.
Do you want to see some of the scammers that have been arrested? Click here to visit www.scammerphotos.com (the SCARS Photo Gallery website)
Anti-Scam FAQ: What is Artificial Intelligence?
Answer:
Artificial intelligence (AI) refers to the simulation of human intelligence in machines that are programmed to think and act like humans. These intelligent machines are able to perform tasks that typically require human cognition, such as problem-solving, decision-making, and learning. AI is a rapidly evolving field that has the potential to revolutionize many aspects of our lives, from healthcare and transportation to education and entertainment. The goal of AI research is to create systems that can process information, reason logically, and learn from experience in order to improve their performance on a wide range of tasks.
This was written by SCARS own AI named “John”
♦ If you have questions for SCARS you can send them to us by email to question@AgainstScams.org or in a message to one of our sites or Facebook pages!
Anti-Scam FAQ: What Is An ATM & Credit Card Shimmer Scam
Answer:
Text
SCARS™ Anti-Scam FAQ: ATM Jackpotting
Scam FAQ: How To Avoid An Auction Scam Or Fraud
- Before you bid, contact the seller with any questions you have.
- Review the seller’s feedback.
- Be cautious when dealing with individuals outside of your own country.
- Ensure you understand refund, return, and warranty policies.
- Determine the shipping charges before you buy.
- Be wary if the seller only accepts wire transfers or cash.
- If an escrow service is used, ensure it is legitimate.
- Consider insuring your item.
- Be cautious of unsolicited offers.
Anti-Scam FAQ: What Is An Authorized Push Payment Fraud
Answer:
Authorized push payment fraud (APP fraud) is a form of fraud in which victims are manipulated into making real-time payments to fraudsters, typically by social engineering attacks involving impersonation. As of 2019 in the United Kingdom, because the victims of these frauds authorized the payments, albeit mistakenly, they are typically not fully reimbursed by their banks.
Scam FAQ: How To Avoid Bogus Employment/Business Opportunities
- Be wary of inflated claims of product effectiveness.
- Be cautious of exaggerated claims of possible earnings or profits.
- Beware when money is required up front for instructions or products.
- Be leery when the job posting claims “no experience necessary”.
- Do not give your social security number when first interacting with your prospective employer.
- Be cautious when dealing with individuals outside of your own country.
- Be wary when replying to unsolicited emails for work-at-home employment.
- Research the company to ensure they are authentic.
- Contact the Better Business Bureau to determine the legitimacy of the company.
Scam FAQ: How To Avoid Credit Card Fraud
- Ensure a site is secure and reputable before providing your credit card number online.
- Don’t trust a site just because it claims to be secure.
- If purchasing merchandise, ensure it is from a reputable source.
- Promptly reconcile credit card statements to avoid unauthorized charges.
- Do your research to ensure the legitimacy of the individual or company.
- Beware of providing credit card information when requested through unsolicited emails.
Anti-Scam FAQ: What is a social engineering attack?
Answer:
In a social engineering attack, an attacker uses human interaction (social skills) to obtain or compromise information about an organization or its computer systems. An attacker may seem unassuming and respectable, possibly claiming to be a new employee, repair person, or researcher and even offering credentials to support that identity. However, by asking questions, he or she may be able to piece together enough information to infiltrate an organization’s network. If an attacker is not able to gather enough information from one source, he or she may contact another source within the same organization and rely on the information from the first source to add to his or her credibility.
What is a phishing attack?
Phishing is a form of social engineering. Phishing attacks use email or malicious websites to solicit personal information by posing as a trustworthy organization. For example, an attacker may send an email seemingly from a reputable credit card company or financial institution that requests account information, often suggesting that there is a problem. When users respond with the requested information, attackers can use it to gain access to the accounts.
Phishing attacks may also appear to come from other types of organizations, such as charities. Attackers often take advantage of current events and certain times of the year, such as
- Natural disasters (e.g., Hurricane Katrina, Indonesian tsunami)
- Epidemics and health scares (e.g., H1N1, COVID-19)
- Economic concerns (e.g., IRS scams)
- Major political elections
- Holidays
What is a vishing attack?
Vishing is the social engineering approach that leverages voice communication. This technique can be combined with other forms of social engineering that entice a victim to call a certain number and divulge sensitive information. Advanced vishing attacks can take place completely over voice communications by exploiting Voice over Internet Protocol (VoIP) solutions and broadcasting services. VoIP easily allows caller identity (ID) to be spoofed, which can take advantage of the public’s misplaced trust in the security of phone services, especially landline services. Landline communication cannot be intercepted without physical access to the line; however, this trait is not beneficial when communicating directly with a malicious actor.
What is a smishing attack?
Smishing is a form of social engineering that exploits SMS, or text, messages. Text messages can contain links to such things as webpages, email addresses or phone numbers that when clicked may automatically open a browser window or email message or dial a number. This integration of email, voice, text message, and web browser functionality increases the likelihood that users will fall victim to engineered malicious activity.
What are common indicators of phishing attempts?
- Suspicious sender’s address. The sender’s address may imitate a legitimate business. Cybercriminals often use an email address that closely resembles one from a reputable company by altering or omitting a few characters.
- Generic greetings and signature. Both a generic greeting—such as “Dear Valued Customer” or “Sir/Ma’am”—and a lack of contact information in the signature block are strong indicators of a phishing email. A trusted organization will normally address you by name and provide their contact information.
- Spoofed hyperlinks and websites. If you hover your cursor over any links in the body of the email, and the links do not match the text that appears when hovering over them, the link may be spoofed. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net). Additionally, cybercriminals may use a URL shortening service to hide the true destination of the link.
- Spelling and layout. Poor grammar and sentence structure, misspellings, and inconsistent formatting are other indicators of a possible phishing attempt. Reputable institutions have dedicated personnel that produce, verify, and proofread customer correspondence.
- Suspicious attachments. An unsolicited email requesting a user download and open an attachment is a common delivery mechanism for malware. A cybercriminal may use a false sense of urgency or importance to help persuade a user to download or open an attachment without examining it first.
How do you avoid being a victim?
- Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about employees or other internal information. If an unknown individual claims to be from a legitimate organization, try to verify his or her identity directly with the company.
- Do not provide personal information or information about your organization, including its structure or networks, unless you are certain of a person’s authority to have the information.
- Do not reveal personal or financial information in email, and do not respond to email solicitations for this information. This includes following links sent in email.
- Don’t send sensitive information over the internet before checking a website’s security.
- Pay attention to the Uniform Resource Locator (URL) of a website. Look for URLs that begin with “https”—an indication that sites are secure—rather than “http.”
- Look for a closed padlock icon—a sign your information will be encrypted.
- If you are unsure whether an email request is legitimate, try to verify it by contacting the company directly. Do not use your contact information provided on a website connected to the request; instead, check previous statements for contact information. Information about known phishing attacks is also available online from groups such as the Anti-Phishing Working Group. (See the APWG eCrime Research Papers).
- Install and maintain anti-virus software, firewalls, and email filters to reduce some of this traffic.
- Take advantage of any anti-phishing features offered by your email client and web browser.
- Enforce multi-factor authentication (MFA).
What do you do if you think you are a victim?
- If you believe you might have revealed sensitive information about your organization, report it to the appropriate people within the organization, including network administrators. They can be alert for any suspicious or unusual activity.
- If you believe your financial accounts may be compromised, contact your financial institution immediately and close any accounts that may have been compromised. Watch for any unexplainable charges to your account.
- Immediately change any passwords you might have revealed. If you used the same password for multiple resources, make sure to change it for each account, and do not use that password in the future.
- Watch for other signs of identity theft.
- Consider reporting the attack to the police, and file a report with the Federal Trade Commission.
Scam FAQ: How To Avoid Phishing/Spoofing Scams
- Be suspicious of any unsolicited email requesting personal information.
- Avoid filling out forms in email messages that ask for personal information.
- Always compare the link in the email to the link that you are actually directed to.
- Log on to the official website, instead of “linking” to it from an unsolicited email.
- Contact the actual business that supposedly sent the email to verify if the email is genuine.
Scam FAQ: How To Avoid BEC Business Email Compromise Scams
- Be mindful of any email, phone call or text messages requesting multiple gift cards even if the request is ordinary.
- Beware of sudden changes in business or personal practices and carefully scrutinize all requests for multiple gift card purchases even if requests are ordinary.
- Since many of the fraudulent e-mails reported in this new trend are spoofed, confirm requests for the purchase of gift cards using two-factor authentication. If using phone verification, use previously known numbers, not the numbers provided in the e-mail request.
Anti-Scam FAQ: What is active content?
Answer:
To increase functionality or add design embellishments, websites often rely on scripts that execute programs within the web browser. This active content can be used to create “splash pages” or options like drop-down menus. Unfortunately, these scripts are often a way for attackers to download or execute malicious code on a user’s computer.
- JavaScript – JavaScript is just one of many web scripts (other examples are VBScript, ECMAScript, and JScript) and is probably the most recognized. Used on almost every website now, JavaScript and other scripts are popular because users expect the functionality and “look” that it provides, and it’s easy to incorporate (many common software programs for building websites have the capability to add JavaScript features with little effort or knowledge required of the user). However, because of these reasons, attackers can manipulate it to their own purposes. A popular type of attack that relies on JavaScript involves redirecting users from a legitimate website to a malicious one that may download viruses or collect personal information.
- Java and ActiveX controls – Different from JavaScript, Java and ActiveX controls are actual programs that reside on your computer or can be downloaded over the network into your browser. If executed by attackers, untrustworthy ActiveX controls may be able to do anything on your computer that you can do (such as running spyware and collecting personal information, connecting to other computers, and potentially doing other damage). Java applets usually run in a more restricted environment, but if that environment isn’t secure, then malicious Java applets may create opportunities for an attack as well.
JavaScript and other forms of active content are not always dangerous, but they are common tools for attackers. You can prevent active content from running in most browsers, but realize that the added security may limit functionality and break features of some sites you visit. Before clicking on a link to a website that you are not familiar with or do not trust, take the precaution of disabling active content.
These same risks may also apply to the email program you use. Many email clients use the same programs such as web browsers to display HTML, so vulnerabilities that affect active content like JavaScript and ActiveX often apply to email. Viewing messages as plain text may resolve this problem.
What are cookies?
When you browse the Internet, information about your computer may be collected and stored. This information might be general information about your computer (such as IP address, the domain you used to connect (e.g., .edu, .com, .net), and the type of browser you used). It might also be more specific information about your browsing habits (such as the last time you visited a particular website or your personal preferences for viewing that site).
Cookies can be saved for varying lengths of time:
- Session Cookies – Session cookies store information only as long as you’re using the browser; once you close the browser, the information is erased. The primary purpose of session cookies is to help with navigation, such as by indicating whether or not you’ve already visited a particular page and retaining information about your preferences once you’ve visited a page.
- Persistent cookies – Persistent cookies are stored on your computer so that your personal preferences can be retained. In most browsers, you can adjust the length of time that persistent cookies are stored. It is because of these cookies that your email address appears by default when you open your Yahoo! or Hotmail email account or your personalized home page appears when you visit your favorite online merchant. If an attacker gains access to your computer, he or she may be able to gather personal information about you through these files.
To increase your level of security, consider adjusting your privacy and security settings to block or limit cookies in your web browser. To make sure that other sites are not collecting personal information about you without your knowledge, choose to only allow cookies for the website you are visiting; block or limit cookies from a third-party. If you are using a public computer, you should make sure that cookies are disabled to prevent other people from accessing or using your personal information.
Anti-Scam FAQ: What Are Brute Force Attack
Answer:
According to information derived from FBI investigations, malicious cyber actors are increasingly using a style of brute force attack known as password spraying against organizations in the United States and abroad.
On February 2018, the Department of Justice in the Southern District of New York, indicted nine Iranian nationals, who were associated with the Mabna Institute, for computer intrusion offenses related to activity described in this report. The techniques and activity described herein, while characteristic of Mabna actors, are not limited solely to use by this group.
The Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI) are releasing this Alert to provide further information on this activity.
Description
In a traditional brute-force attack, a malicious actor attempts to gain unauthorized access to a single account by guessing the password. This can quickly result in a targeted account getting locked-out, as commonly used account-lockout policies allow three to five bad attempts during a set period of time. During a password-spray attack (also known as the “low-and-slow” method), the malicious actor attempts a single password against many accounts before moving on to attempt a second password, and so on. This technique allows the actor to remain undetected by avoiding rapid or frequent account lockouts.
Password spray campaigns typically target single sign-on (SSO) and cloud-based applications utilizing federated authentication protocols. An actor may target this specific protocol because federated authentication can help mask malicious traffic. Additionally, by targeting SSO applications, malicious actors hope to maximize access to intellectual property during a successful compromise.
Email applications are also targeted. In those instances, malicious actors would have the ability to utilize inbox synchronization to:
- obtain unauthorized access to the organization’s email directly from the cloud,
- subsequently download user mail to locally stored email files,
- identify the entire company’s email address list, and/or
- surreptitiously implements inbox rules for the forwarding of sent and received messages.
Technical Details
Traditional tactics, techniques, and procedures (TTPs) for conducting the password-spray attacks are as follows:
- Using social engineering tactics to perform online research (i.e., Google search, LinkedIn, etc.) to identify target organizations and specific user accounts for initial password spray
- Using easy-to-guess passwords (e.g., “Winter2018”, “Password123!”) and publicly available tools, execute a password spray attack against targeted accounts by utilizing the identified SSO or web-based application and federated authentication method
- Leveraging the initial group of compromised accounts, downloading the Global Address List (GAL) from a target’s email client, and performing a larger password spray against legitimate accounts
- Using the compromised access, attempting to expand laterally (e.g., via Remote Desktop Protocol) within the network, and performing mass data exfiltration using File Transfer Protocol tools such as FileZilla
Indicators of a password spray attack include:
- A massive spike in attempted logons against the enterprise SSO portal or web-based application;
- Using automated tools, malicious actors attempt thousands of logons, in rapid succession, against multiple user accounts at a victim enterprise, originating from a single IP address and computer (e.g., a common User Agent String).
- Attacks have been seen to run for over two hours.
- Employee logons from IP addresses resolving to locations inconsistent with their normal locations.
Typical Victim Environment
The vast majority of known password spray victims share some of the following characteristics:
- Use SSO or web-based applications with federated authentication method
- Lack multifactor authentication (MFA)
- Allow easy-to-guess passwords (e.g., “Winter2018”, “Password123!”)
- Use inbox synchronization, allowing email to be pulled from cloud environments to remote devices
- Allow email forwarding to be setup at the user level
- Limited logging setup creating difficulty during post-event investigations
Impact
A successful network intrusion can have severe impacts, particularly if the compromise becomes public and sensitive information is exposed. Possible impacts include:
- Temporary or permanent loss of sensitive or proprietary information;
- Disruption to regular operations;
- Financial losses incurred to restore systems and files; and
- Potential harm to an organization’s reputation.
Solution
Recommended Mitigations
To help deter this style of attack, the following steps should be taken:
- Enable MFA and review MFA settings to ensure coverage over all active, internet facing protocols.
- Review password policies to ensure they align with the latest NIST guidelines and deter the use of easy-to-guess passwords.
- Review IT helpdesk password management related to initial passwords, password resets for user lockouts, and shared accounts. IT helpdesk password procedures may not align to company policy, creating an exploitable security gap.
- Many companies offer additional assistance and tools the can help detect and prevent password spray attacks, such as the Microsoft blog released on March 5, 2018.
Reporting Notice
The FBI encourages recipients of this document to report information concerning suspicious or criminal activity to their local FBI field office or the FBI’s 24/7 Cyber Watch (CyWatch). Field office contacts can be identified at www.fbi.gov/contact-us/field. CyWatch can be contacted by phone at (855) 292-3937 or by e-mail at CyWatch@ic.fbi.gov. When available, each report submitted should include the date, time, location, type of activity, number of people, and type of equipment used for the activity, the name of the submitting company or organization, and a designated point of contact. Press inquiries should be directed to the FBI’s national Press Office at npo@ic.fbi.gov or (202) 324-3691.
Anti-Scam FAQ: Can You File A Lawsuit Against Your Scammer & Money Mule
Answer: In Most Cases Yes
But it very much depends on your country and state or province.
Anti-Scam FAQ: Can Your Personality Make You More Vulnerable To Scams?
Answer: Yes, Very Much So!
SCARS™ Anti-Scam FAQ: Car Scams
The FBI shared information on a growing scam in which crooks target people looking to buy cars and other vehicles online. The FBI has received 26,967 complaints with losses totaling $54,032,396 since tracking this issue from May 2014 through December 2017. This car scamstarts with a criminal posting an online advertisement with a low price to get the attention of a buyer, including photos of the vehicle and contact information. When a buyer reaches out, the “seller” sends more photos and what appears as a logical reason why the price is discounted and indicates a need to sell.
The criminal then instructs you to purchase prepaid gift cards in the amount of the sale and share the prepaid codes. You’re usually told you’ll receive the vehicle in a couple of days, but victims never hear from the scammers again.
Anti-Scam FAQ: What Is A Census-Related Fraud/Scam
Answer:
Census scams happen when someone pretends to work for the Census Bureau to steal your personal information. Use this information to learn how these scams work, and protect yourself against them.
Some scam artists may pretend to be work for the Census Bureau. They’ll try to collect your personal information to use for fraud or to steal your identity. These scam artists may send you letters that seem to come from the U.S. Census Bureau. Others may come to your home to collect information about you.
Anti-Scam FAQ: Why you need strong passwords
Answer:
You probably use personal identification numbers (PINs), passwords, or passphrases every day: from getting money from the ATM or using your debit card in a store, to logging in to your email or into an online retailer. Tracking all of the number, letter, and word combinations may be frustrating, but these protections are important because hackers represent a real threat to your information. Often, an attack is not specifically about your account, but about using access to your information to launch a larger attack.
One of the best ways to protect information or physical property is to ensure that only authorized people have access to it. Verifying that those requesting access are the people they claim to be is the next step. This authentication process is more important and more difficult in the cyber world. Passwords are the most common means of authentication, but only work if they are complex and confidential. Many systems and services have been successfully breached because of non-secure and inadequate passwords. Once a system is compromised, it is open to exploitation by other unwanted sources.
How to choose good passwords
Avoid common mistakes
Most people use passwords that are based on personal information and are easy to remember. However, that also makes it easier for an attacker to crack them. Consider a four-digit PIN. Is yours a combination of the month, day, or year of your birthday? Does it contain your address or phone number? Think about how easy it is to find someone’s birthday or similar information. What about your email password—is it a word that can be found in the dictionary? If so, it may be susceptible to dictionary attacks, which attempt to guess passwords based on common words or phrases.
Although intentionally misspelling a word (“daytt” instead of “date”) may offer some protection against dictionary attacks, an even better method is to rely on a series of words and use memory techniques, or mnemonics, to help you remember how to decode it. For example, instead of the password “hoops,” use “IlTpbb” for “[I] [l]ike [T]o [p]lay [b]asket[b]all.” Using both lowercase and capital letters adds another layer of obscurity. Changing the same example used above to “Il!2pBb.” creates a password very different from any dictionary word.
Length and complexity
The National Institute of Standards and Technology (NIST) has developed specific guidelines for strong passwords. According to NIST guidance, you should consider using the longest password or passphrase permissible (8–64 characters) when you can. For example, “Pattern2baseball#4mYmiemale!” would be a strong password because it has 28 characters and includes upper and lowercase letters, numbers, and special characters. You may need to try different variations of a passphrase—for example, some applications limit the length of passwords and some do not accept spaces or certain special characters. Avoid common phrases, famous quotations, and song lyrics.
Dos and don’ts
Once you’ve come up with a strong, memorable password it’s tempting to reuse it—don’t! Reusing a password, even a strong one, endangers your accounts just as much as using a weak password. If attackers guess your password, they would have access to your other accounts with the same password. Use the following techniques to develop unique passwords for each of your accounts:
- Use different passwords on different systems and accounts.
- Use the longest password or passphrase permissible by each password system.
- Develop mnemonics to remember complex passwords.
- Consider using a password manager program to keep track of your passwords. (See more information below.)
- Do not use passwords that are based on personal information that can be easily accessed or guessed.
- Do not use words that can be found in any dictionary of any language.
How to protect your passwords
After choosing a password that’s easy to remember but difficult for others to guess, do not write it down and leave it someplace where others can find it. Writing it down and leaving it on your desk, next to your computer, or, worse, taped to your computer, makes it easily accessible for someone with physical access to your office. Do not tell anyone your passwords, and watch for attackers trying to trick you through phone calls or email messages requesting that you reveal your passwords.
Programs called password managers offer the option to create randomly generated passwords for all of your accounts. You then access those strong passwords with a master password. If you use a password manager, remember to use a strong master password.
Password problems can stem from your web browsers’ ability to save passwords and your online sessions in memory. Depending on your web browsers’ settings, anyone with access to your computer may be able to discover all of your passwords and gain access to your information. Always remember to log out when you are using a public computer (at the library, an internet cafe, or even a shared computer at your office). Avoid using public computers and public Wi-Fi to access sensitive accounts such as banking and email.
There’s no guarantee that these techniques will prevent an attacker from learning your password, but they will make it more difficult.
Don’t forget security basics
- Keep your operating system, browser, and other software up to date.
- Use and maintain antivirus software and a firewall.
- Regularly scan your computer for spyware. (Some antivirus programs incorporate spyware detection.)
- Use caution with email attachments and untrusted links.
- Watch for suspicious activity on your accounts.



![The Normalcy Bias: Understanding the Cognitive Bias that Can Put You in Danger - 2022 [UPDATED 2025] 2023 Congnitive Biases Series Cognitive Bias/Cognitive Biases - The Psychology of Scams - a SCARS Series on RomanceScamsNOW.com](https://romancescamsnow.com/wp-content/uploads/2023/01/2023-Congnitive-Biases-Series.png)